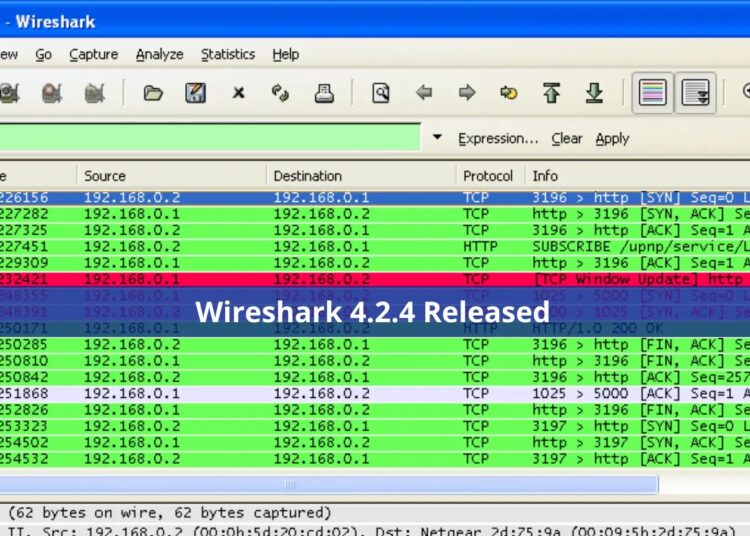
Wireshark remains the go-to choice for both professionals and enthusiasts due to its unmatched capabilities in packet capturing and analysis. Its advanced features and user-friendly interface make it an indispensable tool for network troubleshooting and protocol analysis.
The latest release, Wireshark 4.2.4, brings forth a series of critical updates and bug fixes that underscore the tool’s commitment to providing a robust platform for troubleshooting, analysis, development, and education.
Hosted by the Wireshark Foundation, a nonprofit organization dedicated to promoting protocol analysis education, Wireshark’s newest iteration addresses several vulnerabilities and bugs, ensuring a safer and more efficient environment for its users.
Addressing the Vulnerabilities
One of the highlights of the 4.2.4 release is the resolution of a series of vulnerabilities that could potentially compromise the security of the network analysis process.
Among these, the most notable is the fix for the T.38 dissector crash, identified as issue 19695 and cataloged under CVE-2024-2955. This particular vulnerability posed a significant risk, as it could lead to unexpected crashes, disrupting the analysis workflow and potentially leading to data loss.
In addition to the T.38 dissector crash, Wireshark 4.2.4 also addresses concerns raised by the assignment of CVE-2024-24478, CVE-2024-24479, and CVE-2024-24476.
These vulnerabilities were assigned to Wireshark without prior coordination with the project team. Upon investigation, the Wireshark team determined that each vulnerability was based on invalid assumptions.
As a result, they have requested the rejection of these CVEs, reinforcing the importance of accurate vulnerability reporting and the need for collaboration between security researchers and project teams.
Bug Fixes and Enhancements
Beyond addressing vulnerabilities, Wireshark 4.2.4 introduces several bug fixes aimed at improving the user experience. Among these fixes is the resolution of an issue with Extcap configurations, where users encountered a message stating “Configure all extcaps before start of capture,” preventing the start of data capture. This fix ensures a smoother workflow for users relying on external capture interfaces.
Other notable bug fixes include the resolution of an issue that caused Wireshark to crash when injecting TLS secrets on Windows platforms, and a fix for the packet dissection CSV export feature, which previously included the last column even if it was hidden.
These fixes, along with others addressing crashes and issues identified through fuzz testing, contribute to a more stable and reliable tool for network analysis.
Updated Protocol Support
5GLI, 6LoWPAN, AFP, AllJoyn, AMQP, ASAP, Babel, BACnet, Banana, BEEP, Bencode, BFCP, BGP, BT BNEP, BT SDP, BT-DHT, BVLC, CFLOW, CIP, CMIP, CMP, COROSYNC/TOTEMSRP, COSE, CQL, CSN.1, DAP, DCCP, DCOM, DHCPv6, DICOM, DISP, DOCSIS MAC MGMT, DOF, DVB-S2, E2AP, EDONKEY, ENRP, ErlDP, Etch, EXTREME MESH, FC-SWILS, GIOP, GLOW, GNW, GOOSE, GQUIC, Gryphon, GSM A-bis OML, GSUP, GTPv2, H.223, H.225.0, H.245, H.248, H.264, H.265, HSMS, ICMPv6, ICQ, IEEE1609dot2, IPP, IPPUSB, ISAKMP, iSCSI, ISIS LSP, ISO 7816, ISUP, ITS, JSON 3GPP, JXTA, Kafka, KINK, KNX/IP, LDAP, LDP, LISP, LISP TCP, LLRP, LwM2M-TLV, M2UA, M3UA, MAC-LTE, MBIM, MMS, MONGO, MPEG PES, MPLS Echo, MQ PCF, MQTT-SN, MS-WSP, MSDP, MsgPack, NAS-5GS, NETLINK, NHRP, OpenFlow, OpenWire, OPSI, OSC, P22, P7, PANA, PIM, PNIO, ProtoBuf, PROXY, Q.2931, QNET, RDP, RESP, RPL, RSL, RSVP, RTLS, RTMPT, RTPS, S7COMM, SCTP, SIMULCRYPT, SMB2, SML, SNA, SNMP, Socks, SolarEdge, SOME/IP, SoulSeek, SUA, T.38, TCAP, TEAP, TFTP, Thread, Thrift, TN5250, USBHID, USBVIDEO, VP9, WASSP, WiMAX ASN CP, WLCCP, WTP, X.509IF, X.509SAT, XML, XMPP, YAMI, Z39.50, and ZigBee ZCL
Moving Forward
While the 4.2.4 release does not introduce new or updated capture file support, it does bring updated file format decoding support for BLF, JPEG, and RBM formats. This enhancement broadens the scope of data that can be analyzed within Wireshark, providing users with more flexibility in their analysis tasks.
As Wireshark continues to evolve, the commitment of the Wireshark Foundation and the global community of contributors to addressing vulnerabilities, fixing bugs, and enhancing the tool’s capabilities remains unwavering. With each release, Wireshark reaffirms its position as the world’s most popular network protocol analyzer, essential for anyone engaged in the complex and critical task of network analysis.
For those looking to upgrade or install Wireshark 4.2.4, the software is available for download from the official Wireshark website. As always, users are encouraged to contribute to the project or become sponsors to support the ongoing development and maintenance of this invaluable tool.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here