The automotive industry is experiencing a surge in BEC and VEC attacks, a type of email scam designed to trick employees into transferring money or revealing sensitive information.
A recent incident where a fraudster stole $37 million from Toyota Boshoku by tricking an employee into changing bank account information for a wire transfer shows this rise in attacks.
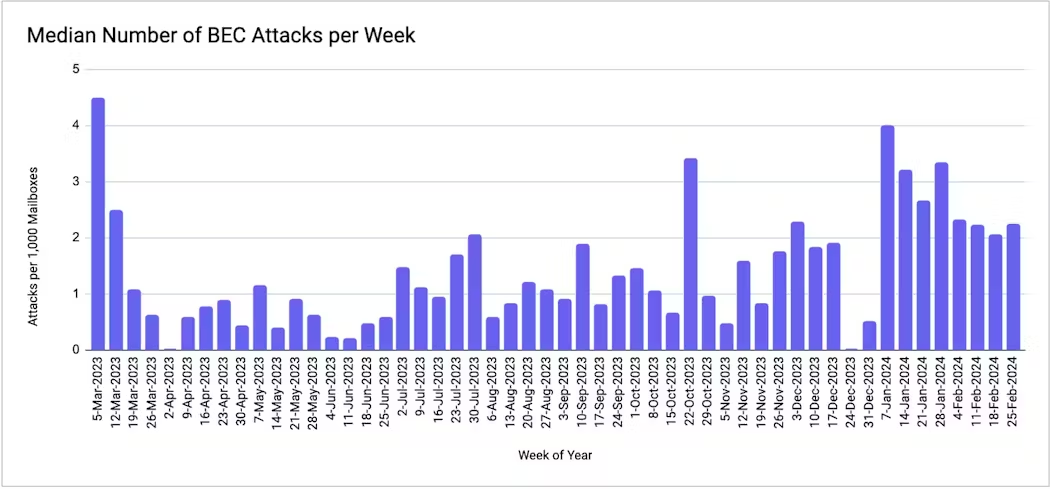
Research suggests that BEC and VEC attacks are on the rise in general, but the automotive industry seems to be a particularly attractive target for cybercriminals.

The automotive industry is experiencing a surge in BEC and VEC attacks due to high-value transactions and complex supply chains with numerous vendors.
Implementing AI-Powered Protection for Business Email Security is an essential component in strengthening the defenses against sophisticated email attacks in the future and enhancing business email.
BEC attacks against automotive businesses rose by 70.5% between September 2023 and February 2024, while 63% of automotive industry customers encountered VEC attacks in the same period. These social engineering attacks bypass traditional security measures, making employees the primary defense.
According to Abnormal Security, attackers impersonate colleagues or vendors via spoofed emails or compromised accounts to trick targets into disclosing sensitive information or initiating unauthorized payments.
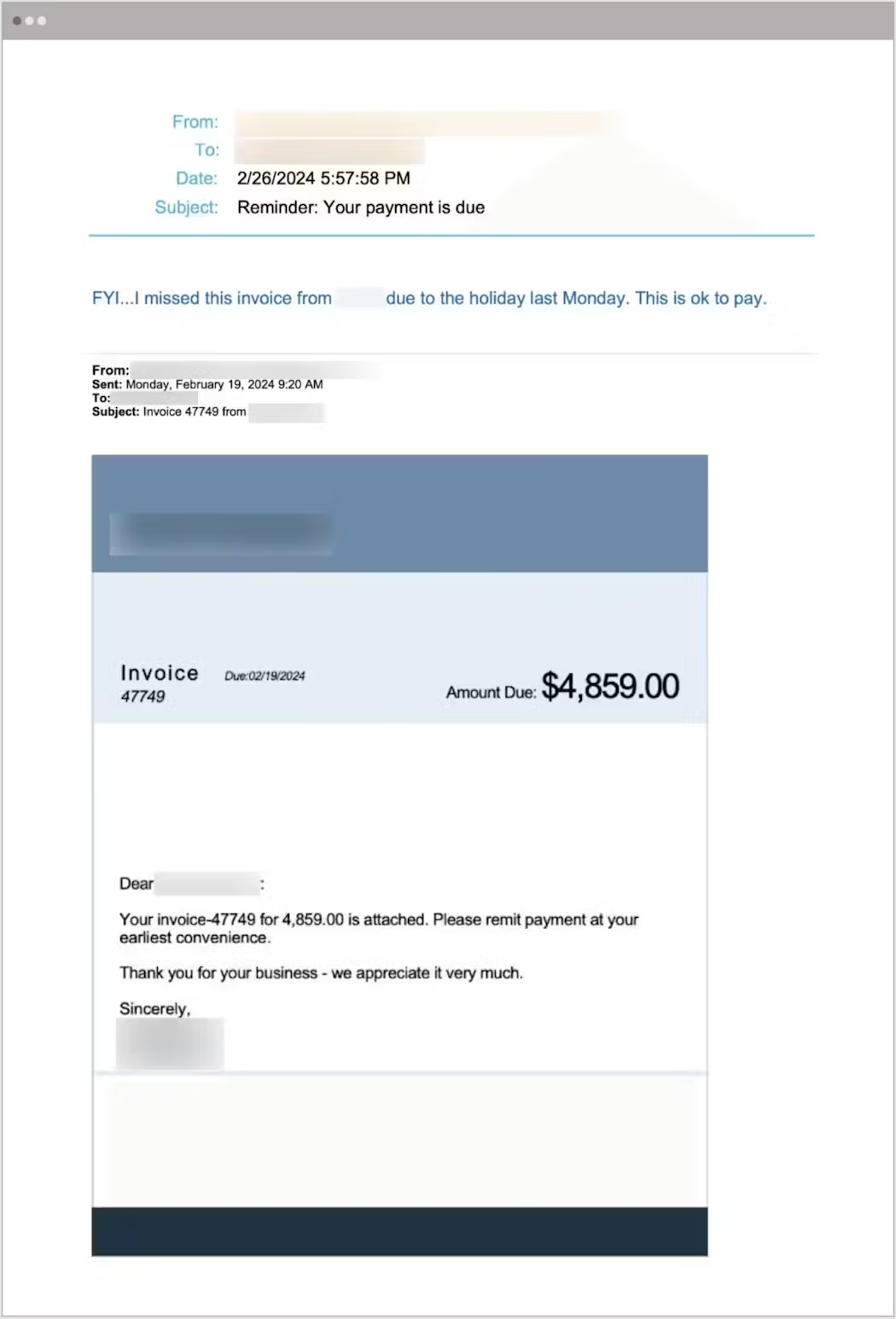
A social engineering attack, masquerading as a Business Email Compromise (BEC), targeted the accounts payable department of a truck dealership, impersonating the company president via email.
The email contained a fabricated invoice from a supposedly legitimate service provider and a forged authorization for payment remittance. An attack uses social engineering to bypass technical security measures by exploiting trust in the sender’s identity and urgency for processing the seemingly approved invoice.
Legacy email security systems are failing to protect automotive organizations from Business Email Compromise (BEC) attacks due to a lack of advanced threat detection and social engineering tactics that exploit familiarity with trusted senders by spoofing email addresses and names.
Traditional email filters rely on identifying malicious attachments or URLs, which are absent in BEC attacks. Consequently, employees are more likely to fall victim to the deceptive nature of these emails.
It highlights the critical need for automotive organizations to implement more sophisticated security solutions to effectively address the evolving threat landscape.
Email-based attacks are on the rise in the auto industry, using social engineering to bypass traditional security solutions.
The attacks lack the usual red flags, like malicious attachments or suspicious URLs, rendering secure email gateways and other legacy tools ineffective, as the human element is now a critical vulnerability that needs to be addressed.
Mitigations:
Email security leader Trustifi’s advanced artificial intelligence engines proactively scan your entire email environment and learn variable behavior patterns common with compromised accounts to stop advanced email-based attacks such as:
- Business email compromise
- Sophisticated phishing attacks
- Advanced malware
- CEO impersonation fraud
- Spoofing attacks
- Vendor email compromise
- Account takeover and compromise
- Behavioral anomalies
- Basic and covert spam and graymail
Opt-in for AI-Powered Protection for Business Email Security You can stop inbound threats and block attackers from reaching User inboxes.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.
Read the full article here

