Mispadu, a banking trojan initially targeting Latin America, has expanded its attacks to Europe, stealing credentials through phishing emails and malicious URLs.
The attackers utilize stolen credentials for further phishing attacks, making it a significant threat.
Despite the geographic expansion, Mexico remains the primary target, with thousands of stolen credentials since April 2023.
The infection chain involves multiple stages, but the main changes occur in the initial stages.
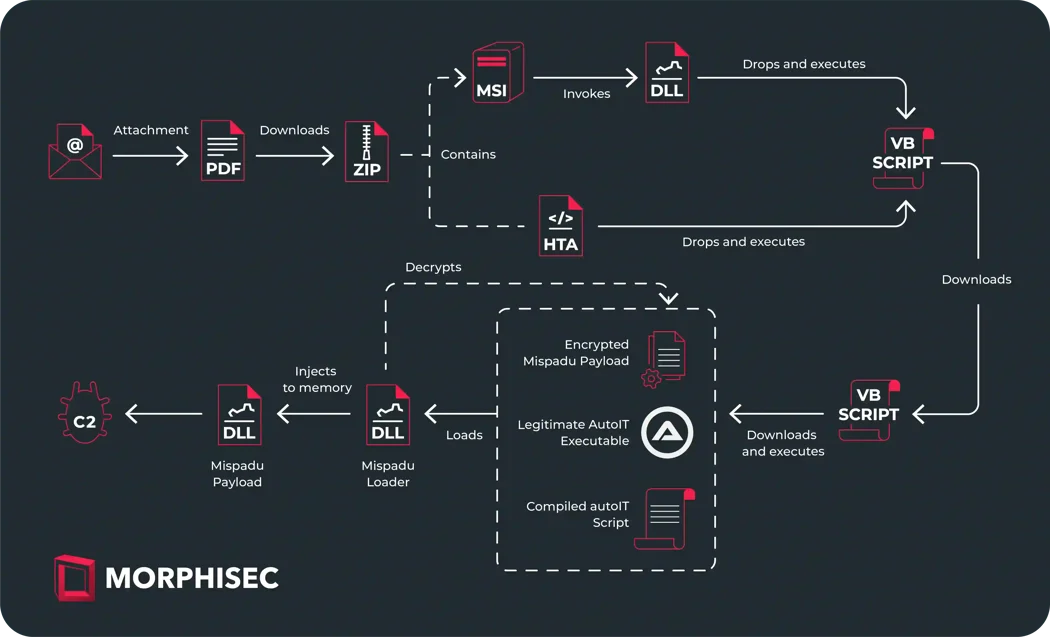
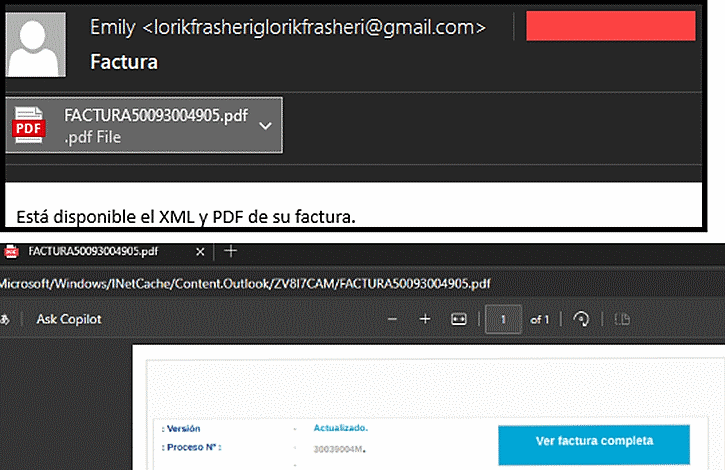
The phishing email pretends to be an invoice notification with a PDF attachment. Clicking a button within the PDF triggers the download of a ZIP file from a shortened URL, which is hosted on a free email service and likely contains the malicious payload, Morphisec said.
VB Script Stages
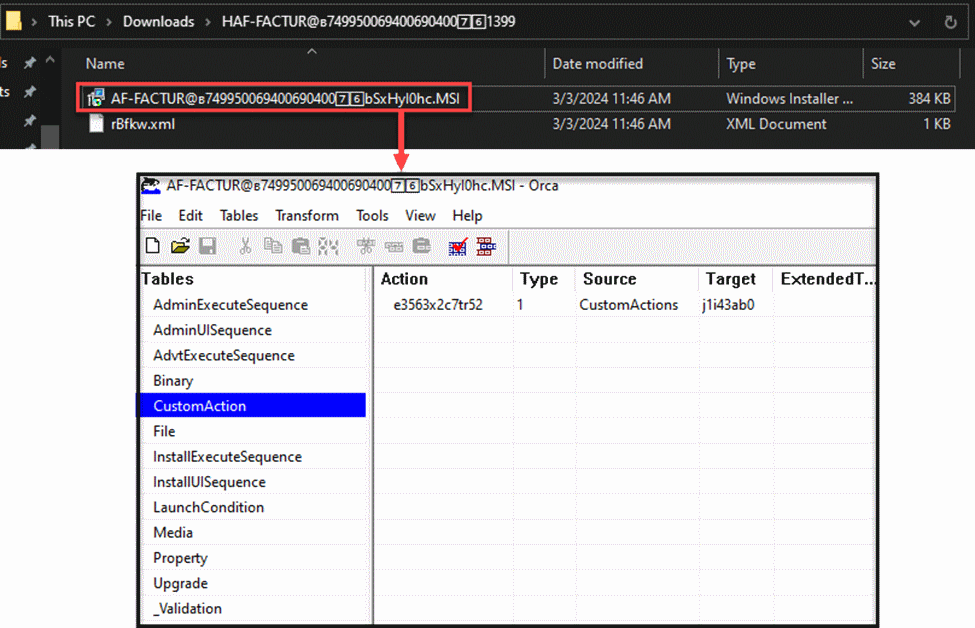
The malware arrives as either an MSI or HTA file, both of which ultimately deploy a first-stage VB script, while the MSI uses a custom DLL function to decrypt a hidden command that drops the script and the HTA also uses a similar command.
To avoid detection, the VB script runs in memory and checks the User-Agent string for “(MSIE)” to confirm that Internet Explorer is running it.

If valid, it contacts a command-and-control server for the next stage payload, which is identical regardless of the initial MSI or HTA infection method.
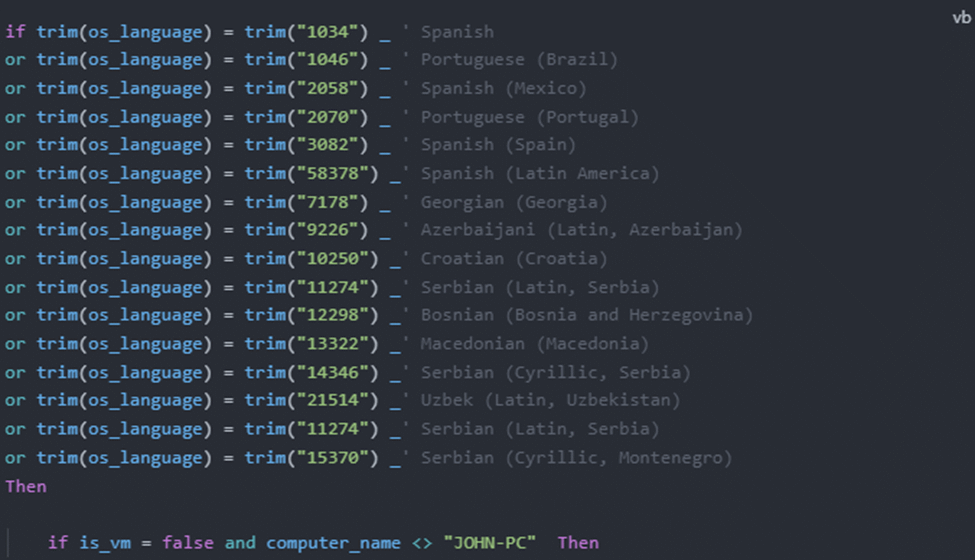
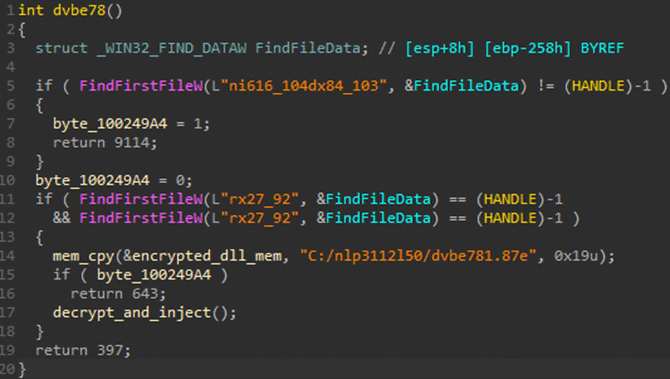
The heavily obfuscated script checks for virtual machines by comparing system data to known virtual machine profiles verifies language, and avoids execution on machines named “JOHN-PC,” and if these checks pass, the script downloads three obfuscated files.
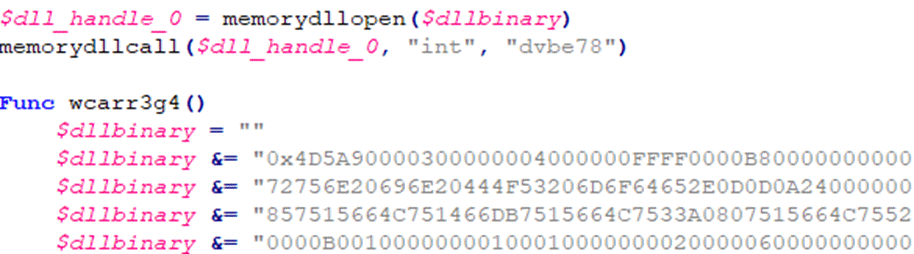
The first decrypts the final Mispadu payload and the second decrypts an archive containing a compiled AutoIT script that, when run by a third downloaded and decrypted legitimate AutoIT executable, loads a DLL, which decrypts and injects the final Mispadu payload into memory, according to Morphisec report.
The decompiled AutoIT script snippet injects malicious code by first loading a DLL containing the decryption logic and decrypting a payload that a VB script had earlier downloaded, it then calls an exported function from the DLL.
The decrypted payload, likely malware, is injected into a legitimate Windows process, either attrib.exe or RegSvcs.exe, which disguises the malicious code and makes it harder to detect.
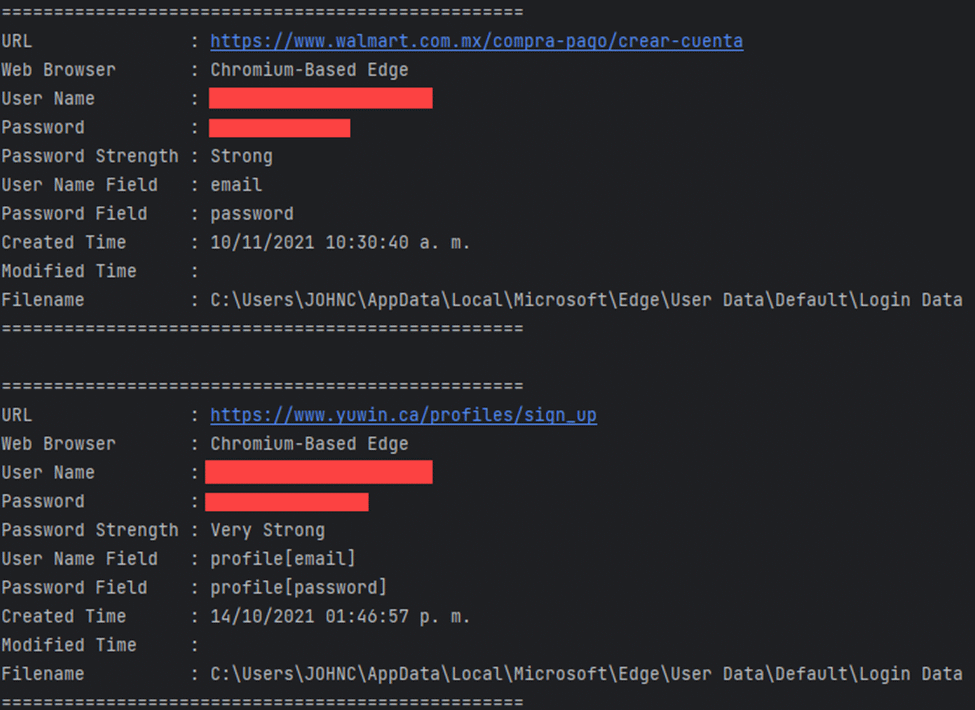
Mispadu’s final payload utilizes legitimate tools, WebBrowserPassView and MailPassView, to steal passwords from web browsers and email clients by actively monitoring user activity and searching for specific strings related to finance and email applications.
It allows it to target over 200 different services for credential theft, while stolen data is uploaded to a command-and-control server (C2) in two parts:
first, email client credentials and browser passwords; second, a list of harvested email addresses, which are then likely weaponized for further phishing attacks.
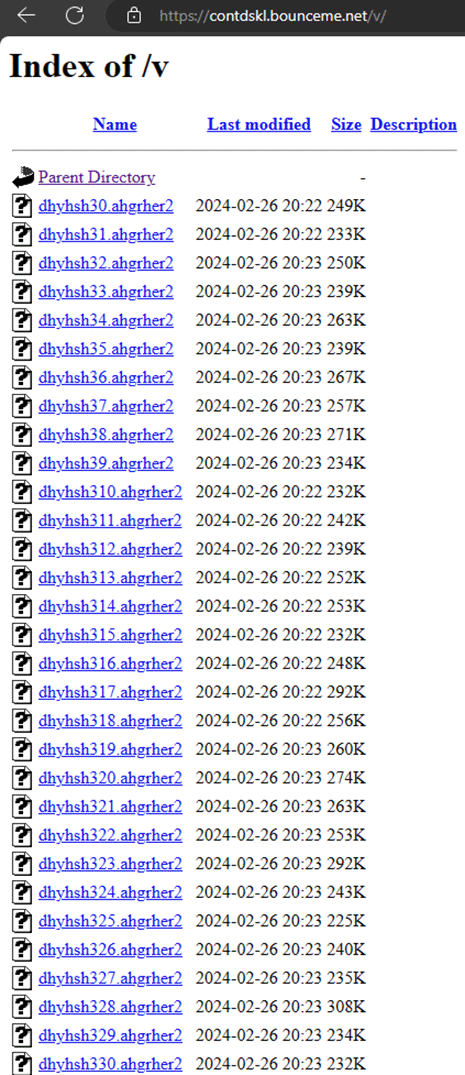
An attacker uses two C2 servers:
one to deliver initial attack payloads and another to steal credentials, where the first server constantly changes, while the exfiltration server remains consistent across campaigns.
Analysis of stolen credentials reveals an ongoing attack since April 2023, with over 60,000 files currently on the exfiltration server.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here