The cybersecurity landscape faces a new threat with the emergence of ‘darcula,’ a Phishing-as-a-Service (PhaaS) platform.
This sophisticated service enables cybercriminals to launch phishing campaigns across over 20,000 domains, using advanced techniques to target over 100 countries.
Unlike traditional phishing kits, ‘darcula’ utilizes modern technology such as JavaScript, React, Docker, and Harbor, akin to the tools used by cutting-edge tech startups.
This allows for seamless updates and the addition of new features and anti-detection measures without the need to reinstall the phishing kit.
The ‘darcula’ platform has adopted unique methods to distribute phishing URLs, particularly through iMessage and RCS (Rich Communication Services), which bypass traditional SMS firewalls.
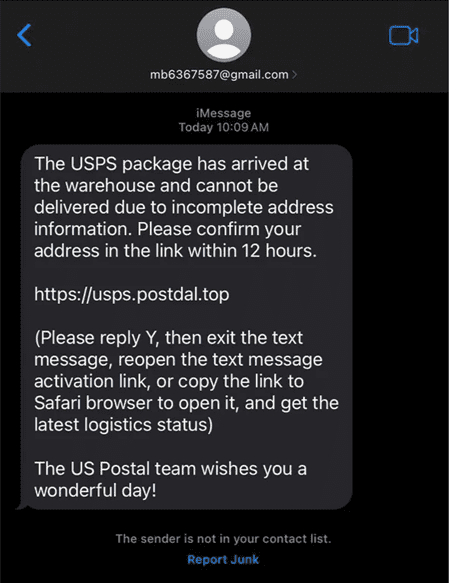
This tactic has proven effective against organizations like the United States Postal Service (USPS) and has been observed in high-profile phishing attacks in the UK and the US.
To find and eradicate sophisticated phishing attacks, Trustifi AI-powered multi-layer email security protects both inbound and outbound emails; Request a Free Quote.
The ‘darcula’ PhaaS Model
Developed by a Telegram user of the same name, ‘darcula’ operates on a subscription-based model. It offers hundreds of phishing site templates that mimic reputable brands.
These templates target postal services as well as financial institutions, government bodies, and other entities that have significant consumer trust.
Dracula phishing attacks typically use purpose-registered domains rather than compromised ones, usually spoofing the relevant brand name.
“The most common top-level domains (TLDs) used for Dracula are .top and .com, followed by numerous low-cost generic TLDs. Cloudflare’s platform is used by 32% of Darcula pages, and Darcula’s documentation recommends Cloudflare’s services to avoid exposing the underlying server’s IP address. Tencent, Quadranet, and Multacom are also common choices.” Netcraft said.
Technical Infrastructure and Anti-Monitoring Techniques
The platform predominantly uses purpose-registered domains, with .top and .com being the most common top-level domains (TLDs). Cloudflare is a popular choice among ‘darcula’ pages, used by 32% to conceal the server’s IP address.
The platform has also implemented cloaking techniques, such as displaying fake domain sale pages, to hinder takedown efforts.
The Role of RCS and iMessage
‘darcula’ leverages RCS and iMessage to send phishing messages, taking advantage of these services’ end-to-end encryption. This instills trust in recipients and circumvents recent legislation aimed at blocking illegal robotext messages.
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated phishing attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
To bypass security measures, such as Apple’s restriction on clicking links from unknown senders, ‘darcula’ prompts users to reply to messages, enabling the links to become clickable.
Countermeasures and Future Implications
Google and Apple have taken steps to combat this phishing, with Google blocking RCS messaging on rooted phones and implementing measures to prevent mass messaging. However, as ‘darcula’ continues to evolve, it poses a significant challenge to cybersecurity efforts worldwide.
In conclusion, the ‘darcula’ PhaaS platform represents a significant evolution in phishing tactics, leveraging modern technology and communication protocols to evade detection and deliver highly effective phishing campaigns. As cybercriminals continue to innovate, organizations and individuals must remain vigilant and adopt robust cybersecurity measures to protect against these sophisticated threats.
Secure your emails in a heartbeat! Take our free 30-second assessment and get matched with your ideal email security vendor. Start now:
Read the full article here

