Glupteba, a decade-old malware in financial cybercrime, unveiled a new campaign in November 2023.
Despite its long tenure, the undiscovered features include a UEFI bootkit that allows stealthy persistence, challenging detection, and removal.
Security analysts at Palo Alto Networks recently discovered Glupteba, which is a multipurpose malware that controls the OS boot process to hide itself.
Multipurpose Glupteba Malware
From a basic backdoor, Glupteba evolved into a powerful botnet that has become a significant power in cyber threats since the early 2010s.
This malware is primarily known for intricate infection chains as it reflects operators’ constant innovations to elude traditional security measures.
Cortex Agent 8.3 introduces UEFI Protection for boot kits like Glupteba by offering detection and prevention.
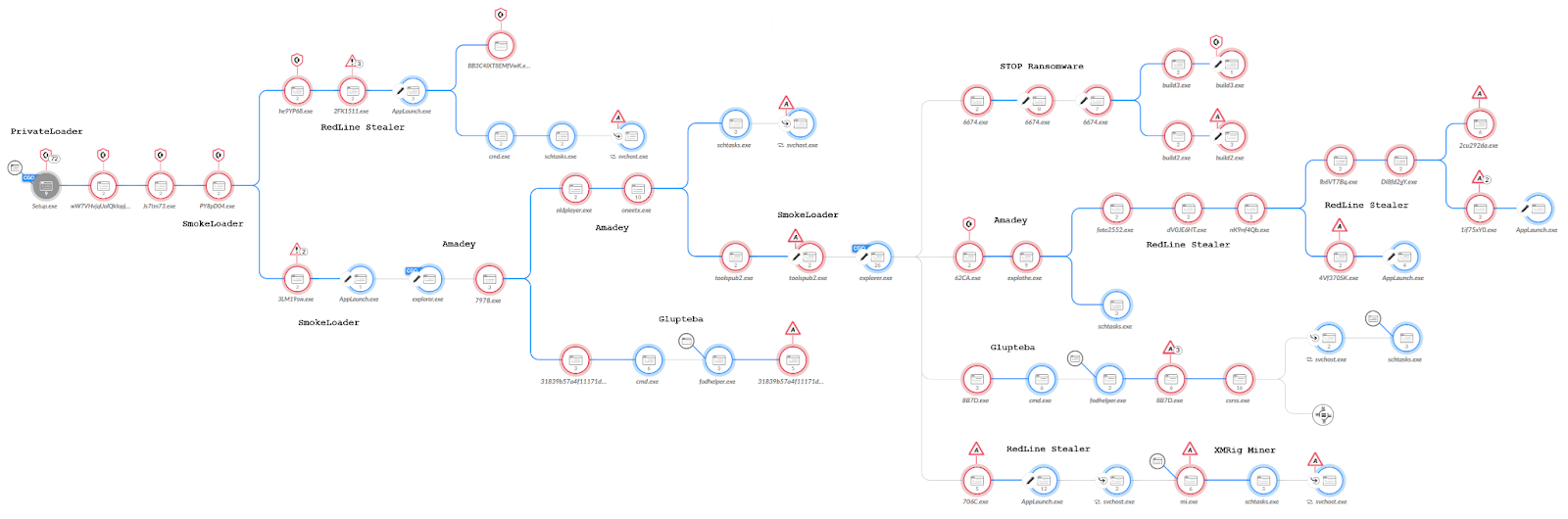
Glupteba’s modular design facilitates additional payloads, making it versatile in various attack settings. At the same time, recent campaigns have used pay-per-install services, which enable widespread global infections.
The PPI ecosystem evolving from ad distribution, as it fuels malware like Glupteba, RedLine Stealer, and ransomware. Key players like Ruzki, run by les0k on Russian forums, enable widespread malware dissemination.
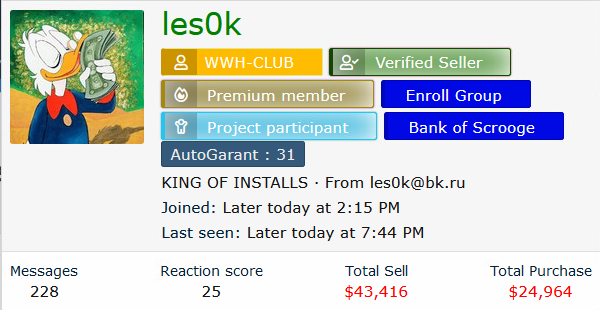
The PPI services lure malware operators with promotions and discounts, pricing based on installations and regions.
Glupteba revived globally in December 2022 after Google’s 2021 disruption, impacting various countries and industries.
Its resurgence involves web-based distribution and phishing attacks that cause widespread infections.
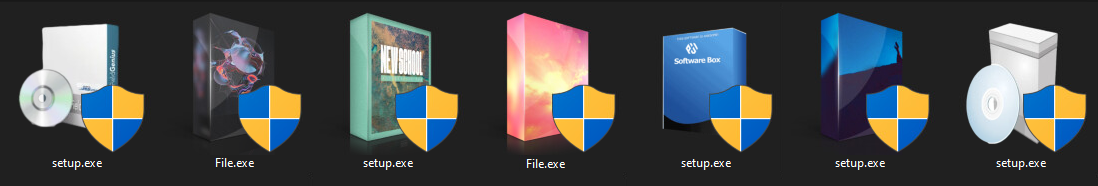
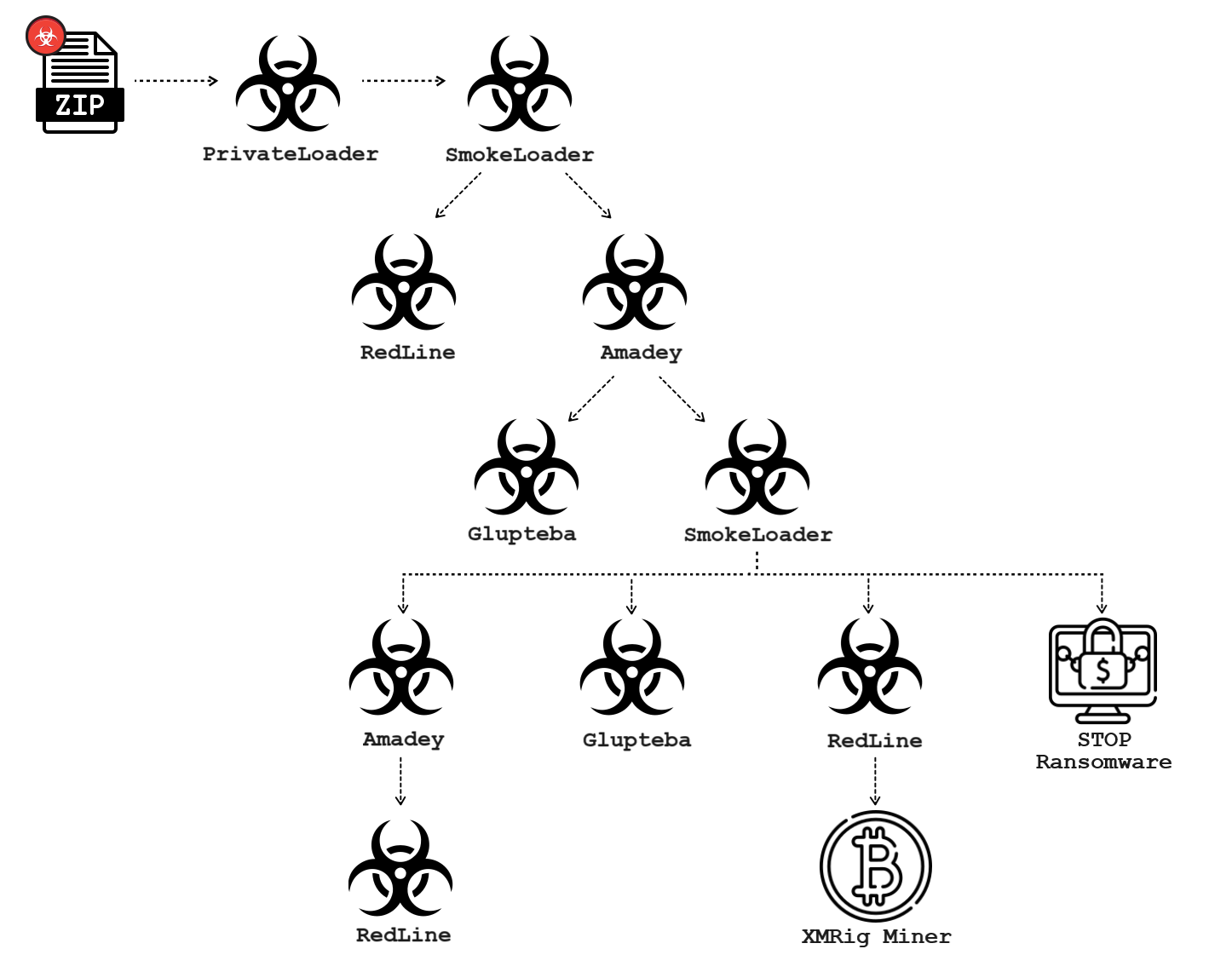
The multi-stage campaign initiates by luring users to download fake installation files. Glupteba spreads through loaders like PrivateLoader or SmokeLoader.
In 2023, multiple chains showed PrivateLoader leading to SmokeLoader and eventually Glupteba. This highlights the malware’s versatility, and not only that, even the analysis unveiled undocumented UEFI bootkit.
UEFI defines computer firmware by handling boot and OS interaction. Pre-boot, firmware loads from SPI flash. The ESP in the boot device with Windows Boot Manager loads during Windows boot.
Malware in ESP disrupts security, and the SPI implant offers more power but needs higher privileges. However, few UEFI boot kits were reported, like LoJax and BlackLotus (2023).
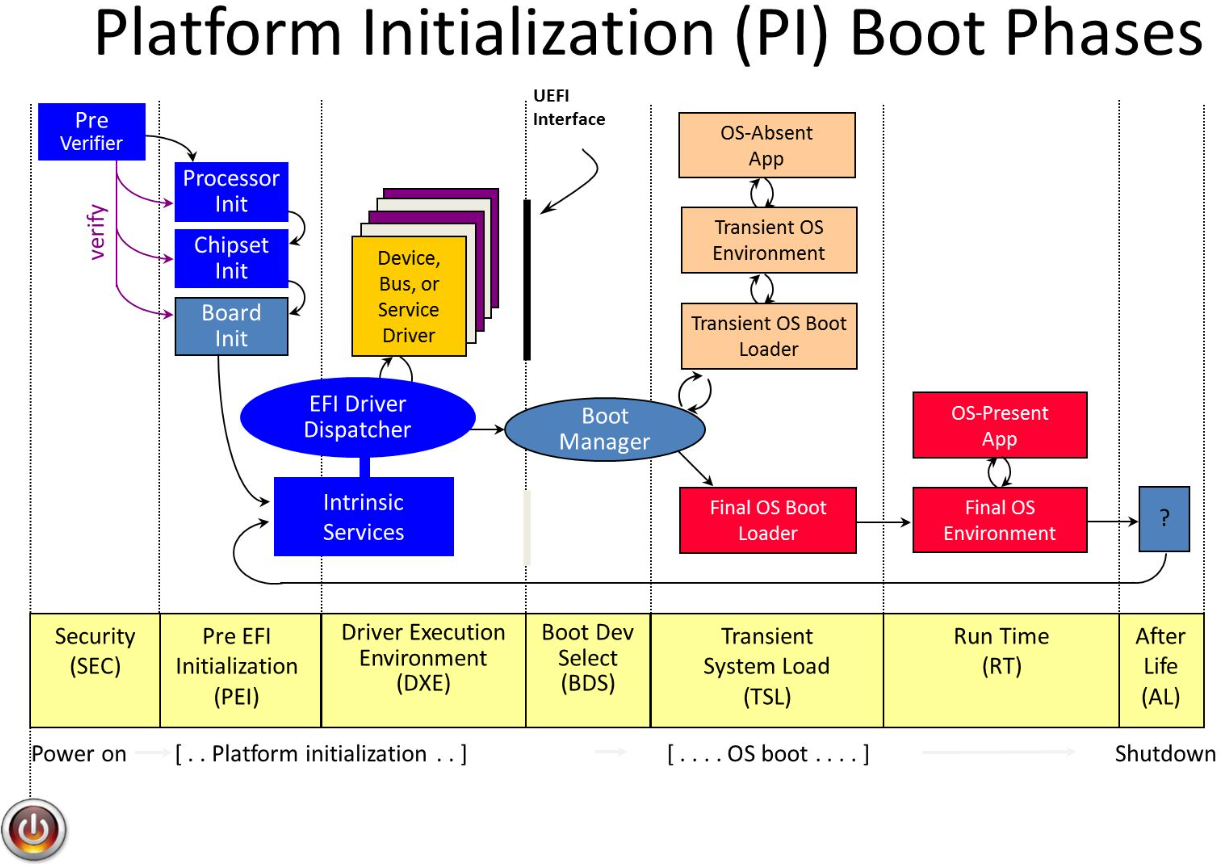
EfiGuard, an open-source UEFI bootkit that patches Windows kernel via EfiGuardDxe.efi by disabling PatchGuard and DSE. EfiGuardDxe.efi runs by installing in UEFI driver entry or using a custom loader (Loader.efi), as Glupteba does.
The driver hooks EFI Boot Service LoadImage function by intercepting the Windows Boot Manager loading (bootmgfw.efi) which initiates a chain of patches to patch the kernel (ntoskrnl.exe).
Glupteba malware showcases modern cyber threats with its innovative UEFI bypass, which challenges detection.
The PPI ecosystem reveals the collaboration between cybercriminals that stresses the need for enhanced cybersecurity strategies beyond the standard defenses.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here