Threat actors have been evading in-built scanners in the cloud and local systems but archiving them as password-protected ZIP files. This makes it hard for scanners to crack the password and scan for malicious files.
However, recent reports suggest that Microsoft can scan password-protected archive files in Sharepoint and check for malware.
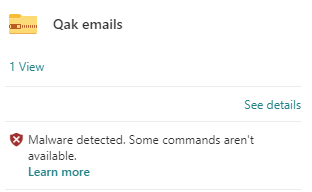
Security researcher Andrew Brandt posted on infosec.exchange platform that Sharepoint has scanned a couple of his archive files and marked them as “Malware Detected”.
He uploaded the files in SharePoint for malware research with the password “infected.” Nevertheless, they were scanned and removed by Microsoft.

In his post, he stated, “This morning, I discovered that a couple of password-protected Zips are flagged as “Malware detected” which limits what I can do with those files – they are basically dead space now.”
On further discussion, it was denoted that Microsoft scans the contents of Password-protected ZIP files using various methods in all of its cloud services.
This feature can be considered as a security measure taken from Microsoft, but as Brandt stated, “The available space to do this just keeps shrinking and it will impact the ability of malware researchers to do their jobs.”
During the conversation, Kevin Beaumont chimed in to mention that Microsoft employs various techniques to scan the contents of password-protected zip files. These methods are not limited to files stored in SharePoint but are applicable across all its 365 cloud services.
According to a Google representative, the company does not scan password-protected zip files. However, Gmail does notify users when they receive such files. Additionally, my work account, managed by Google Workspace, prohibited me from sending a password-protected zip file.
Scanning password-protected files for malicious software is good in a way for users. But for security researchers, it limits them from sharing their malware research data and the malware file with anyone for further analysis.
Microsoft employees were contacted to discuss this issue, which was unsuccessful as they never responded. Users must be vigilant when opening password-protected ZIP files that could potentially contain malware.
Struggling to Apply The Security Patch in Your System? –
Try All-in-One Patch Manager Plus

Read the full article here

