Security researchers have uncovered a critical vulnerability in the Linux kernel’s io_uring subsystem, which could allow attackers to gain full root access to affected systems.
The flaw, tracked as CVE-2024-0582, was found to be particularly exploitable in Ubuntu distributions due to a delay in patching despite the vulnerability being addressed in the stable kernel release in December 2023.
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
CVE-2024-0582: The Use-After-Free Vulnerability
The vulnerability stems from a use-after-free (UAF) condition in the io_uring interface, a feature introduced in Linux kernel version 5.1 to improve the performance of applications with high I/O operations.
Despite its benefits, io_uring has been a hotbed for security vulnerabilities, leading to its restriction or outright disablement in environments like ChromeOS, Google’s production servers, and Android.
CVE-2024-0582 allows an attacker to gain read and write access to previously freed pages, offering a potent exploit primitive far beyond the typical UAF exploit.
This vulnerability was present in Linux kernel versions from 6.4 up to, but not including, 6.7, affecting major Ubuntu releases such as Ubuntu 23.10 and Ubuntu 22.04 LTS.
Exodus Intelligence has recently released a report on a flaw found in the Linux Kernel. The flaw allows an attacker to obtain elevated privileges on a system by exploiting a vulnerability in the Futex subsystem.
Patch Timeline
- December 8, 2023: The vulnerability was patched in the stable kernel release 6.6.5.
- January 8, 2024: The Project Zero issue detailing CVE-2024-0582 was made public.
- February 22, 2024: Ubuntu finally patched the issue in kernel version 6.5.0-21 for Ubuntu 22.04 LTS and Ubuntu 23.10.
CVE-2024-0582’s exploitability lies in its ability to allow data-only exploits, bypassing common exploit mitigations like Control-Flow Integrity (CFI).
Attackers can manipulate data to escalate privileges without altering the code execution flow. This vulnerability was exploited using a data-only strategy, enabling a non-privileged user to achieve root privileges on affected systems.
According to a recent tweet by Cyber Advising, a memory leak vulnerability has been identified as CVE-2024-0582 in the Linux kernel’s io_uring functionality.
The io_uring Interface
io_uring offers a high-performance, asynchronous I/O API, reducing the overhead caused by blocking system calls and data transfers between user and kernel space. However, its complexity has made it a target for vulnerability research.
The io_uring API consists of three system calls:
- io_uring_setup()
- io_uring_register()
- io_uring_enter()
Exploitation Strategy
The exploitation strategy triggered the UAF condition by manipulating io_uring’s provided buffer rings, explicitly using the IOU_PBUF_RING_MMAP flag.
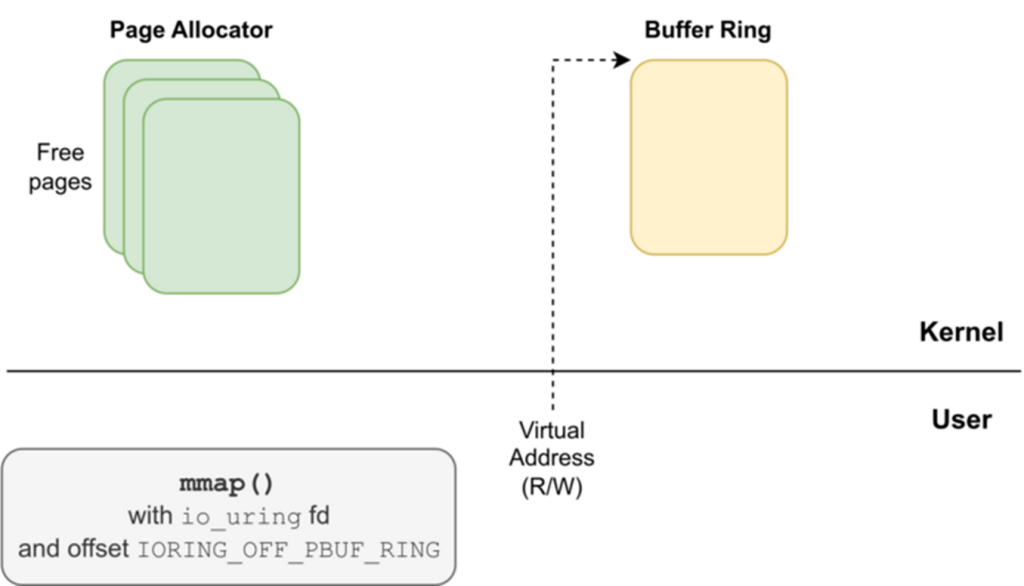
This allowed attackers to retain access to memory pages even after they were freed and reallocated by the kernel for other purposes, such as file structures (struct file).
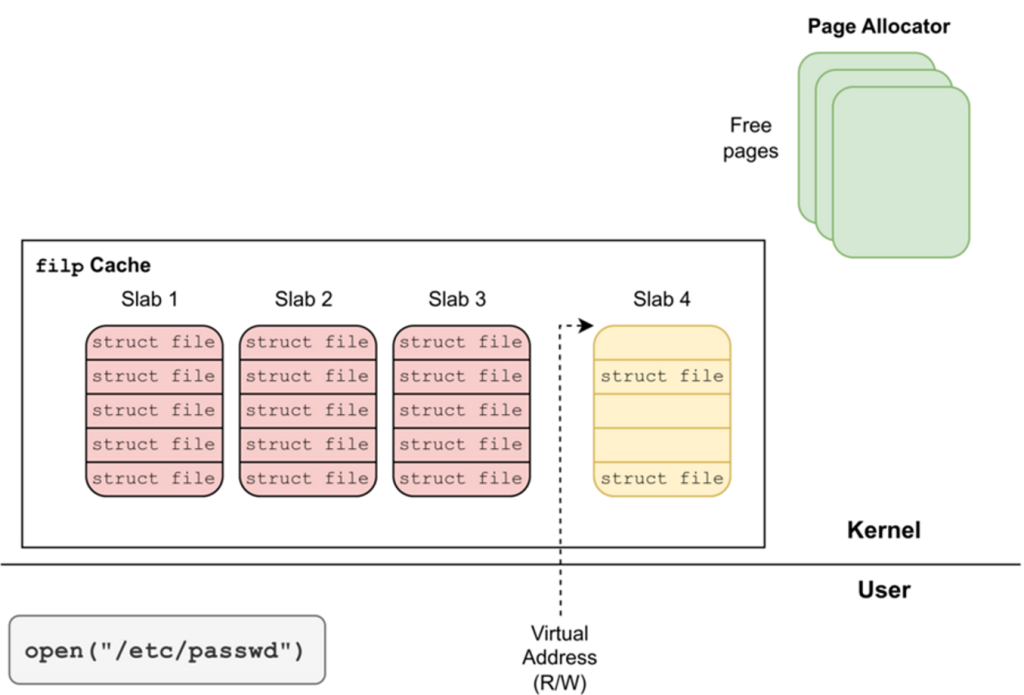
By forcing the allocation of file structures on these controlled pages, attackers could modify critical fields, such as f_mode, to gain writable access to read-only files, including /etc/passwd.
This effectively allowed the addition of a backdoor account with root privileges.
The discovery and exploitation of CVE-2024-0582 highlight significant concerns regarding the security of the io_uring subsystem and the timely patching vulnerabilities in widely used distributions like Ubuntu.
The two-month patch gap for Ubuntu kernels allowed attackers to exploit this vulnerability, underscoring the importance of rapid vulnerability response processes.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here