PuTTY is among the most popular targets of hackers due to several reasons.
Firstly, it is used for remote access to servers and systems at large, hence a great ground for infiltration.
Exploiting vulnerabilities or misconfigurations in PuTTY can expose sensitive data or allow code execution on targeted machines.
By hacking into PuTTY installs, hackers can set up persistent backdoors and transit networks sideways to extend their scope and influence.
Cybersecurity researchers at Malwarebytes Labs recently warned Linux admins of a fake PuTTY client dubbed “Rhadamanthys” Stealer.
Fake PuTTY Client Rhadamanthys Stealer
Hackers utilize malicious advertisements impersonating legitimate software like PuTTY to distribute malware loaders.
These loaders aim to compromise systems and deploy additional payloads while evading detection.
Free Webinar : Mitigating Vulnerability & 0-day Threats
Alert Fatigue that helps no one as security teams need to triage 100s of vulnerabilities.
:
- The problem of vulnerability fatigue today
- Difference between CVSS-specific vulnerability vs risk-based vulnerability
- Evaluating vulnerabilities based on the business impact/risk
- Automation to reduce alert fatigue and enhance security posture significantly
AcuRisQ, which helps you to quantify risk accurately:
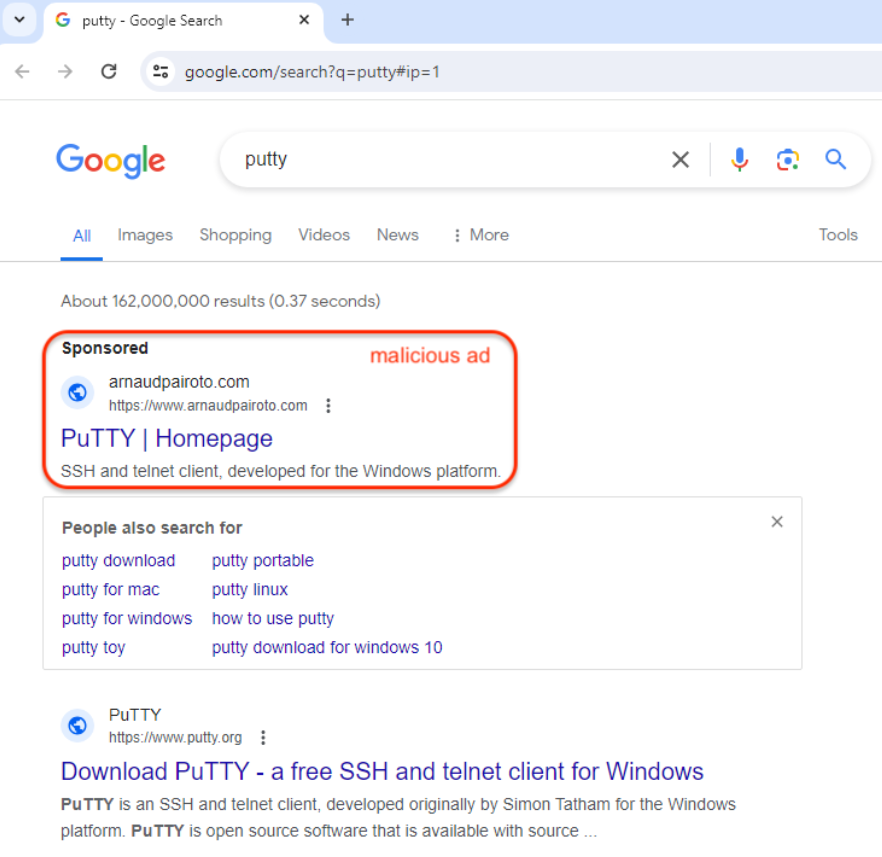
In this case, the threat actor purchased an ad falsely claiming to be the PuTTY homepage, appearing at the top of search results before the official site.
While the unrelated domain raised suspicions here, many advertisements closely mimic trusted brands, making them effective lures for distributing stealthy malware loaders that enable further exploitation.
Potential victims from the United States are redirected to a fake putty.org, while others are shown a legitimate page that bypasses security checks.
This redirection chain is multi-staged and possibly probes for proxies as well as logs victims’ IPs before serving a final malware payload.
Acting like the PuTTY program, this dropper is written in Go, which provides the attackers with an entry point into compromised systems for future exploitation.
The deceptions of such a campaign and the complexity of its payload delivery scheme reveal the extent to which threat actors can spread malware without being noticed.
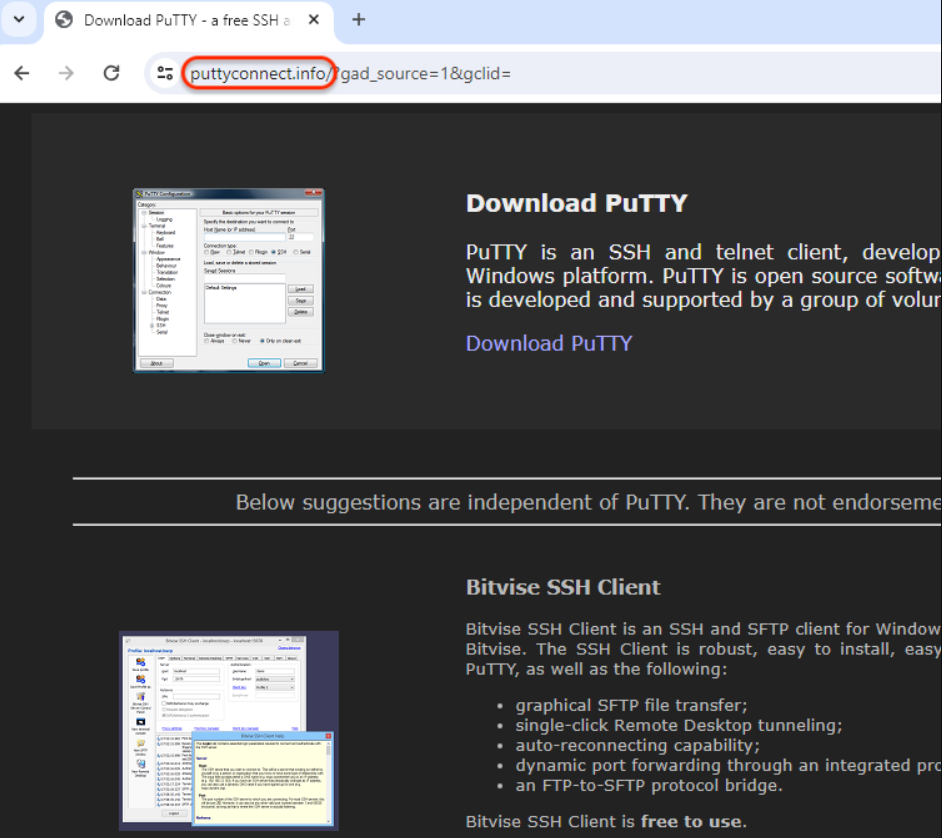
This is done to show that, the victim did follow the deceptive ad campaign and downloaded it from a fake PuTTY site.
In case IP matches, it fetches a follow-on payload from the CnC server; as a result, it further propagates the multi-stage infection chain.
As such, this process of IP verification helps them distinguish potential researchers or honeypots who may have been lured into participating in this campaign.
This keeps additional payloads from being sent to any other system violated through their fraudulent advertisement campaigns.
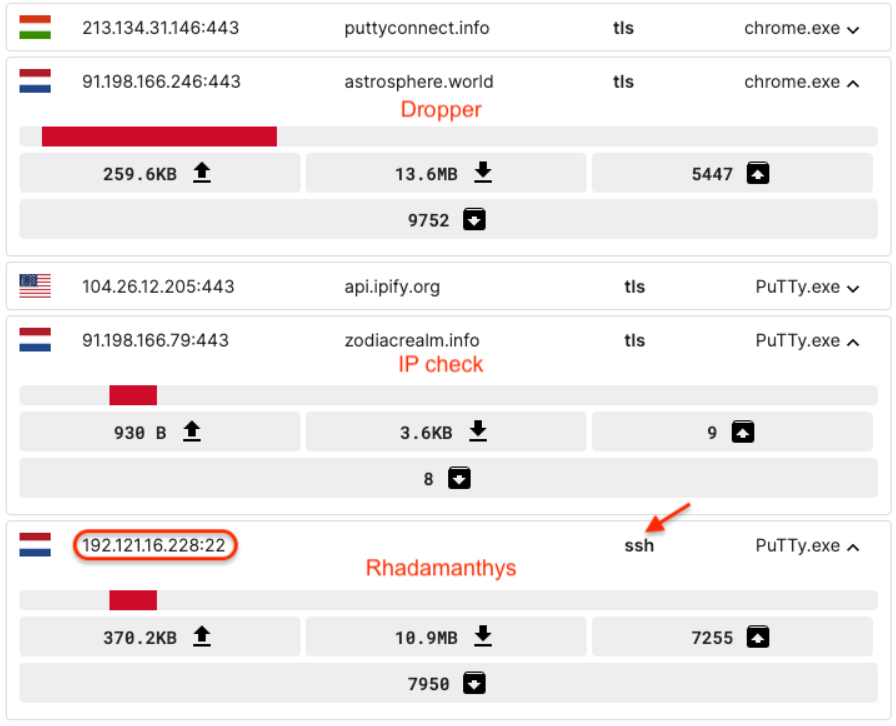
The Go-based dropper uses SSH protocol in secret to pull the following-stage payload, probably Rhadamanthys malware, from some command and control server, reads the report.
This multiple-component infection chain, which offers malware deployment services ranging from malicious ads to loaders and final payloads, demonstrates a sophisticated malvertising infrastructure controlled by the same bad actor.
Although this particular campaign was reported to Google, it shows how threat actors are always changing their techniques to evade security controls.
To counter such stealthy malware distribution schemes, proactive defense mechanisms like strong malware detection and ad-blocking are crucial.
IoCs
Decoy ad domain
Fake site
PuTTY
- astrosphere[.]world
- 0caa772186814dbf84856293f102c7538980bcd31b70c1836be236e9fa05c48d
IP check
Rhadamanthys
- 192.121.16[.]228:22
- bea1d58d168b267c27b1028b47bd6ad19e249630abb7c03cfffede8568749203
With Perimeter81 malware protection, you can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits. All are incredibly harmful and can wreak havoc on your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here