The Nitrogen campaign has been identified as the latest threat vector for malware delivery via malicious search ads. While the tactic of hackers using malicious search ads to distribute malware is not new, this campaign highlights the ongoing need for robust security measures to be implemented in the digital realm.
In the Nitrogen campaign observed by Malwarebytes, the attackers are utilizing hacked WordPress websites as a platform to host the malevolent PHP shell scripts.
Cybercriminals have used BlacKHat SEO tactics to boost their search engine rankings for popular keywords. In their latest campaign, these hackers target WinDirStat, a widely used graphical tool that helps users analyze disk usage on Windows operating systems.
The attackers use sophisticated techniques to manipulate search engine algorithms and direct users to malicious websites that host malware.
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Try Trustifi Free Threat Scan with Sophisticated AI-Powered Email Protection .
Nitrogen Targeting IT & System Admins
The advertisements are exhibited through Google queries for commonly searched keywords regarding software programs utilized by IT professionals and system administrators.
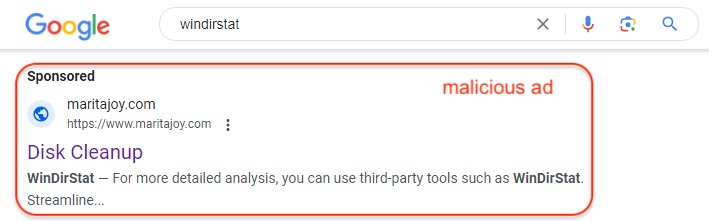
Upon clicking on the ad, the initial step involves visitor filtering. The system examines the client-side settings and IP address, and if it identifies any discrepancies, it redirects the visitor to a fake page to prevent access to the actual content.
If they like the user settings, they will be served a 302 redirect to a decoy site at windirsstat[.]net that looks real.
To deliver the fake software, hackers use multiple numbers of hacked sites on a rotation basis.
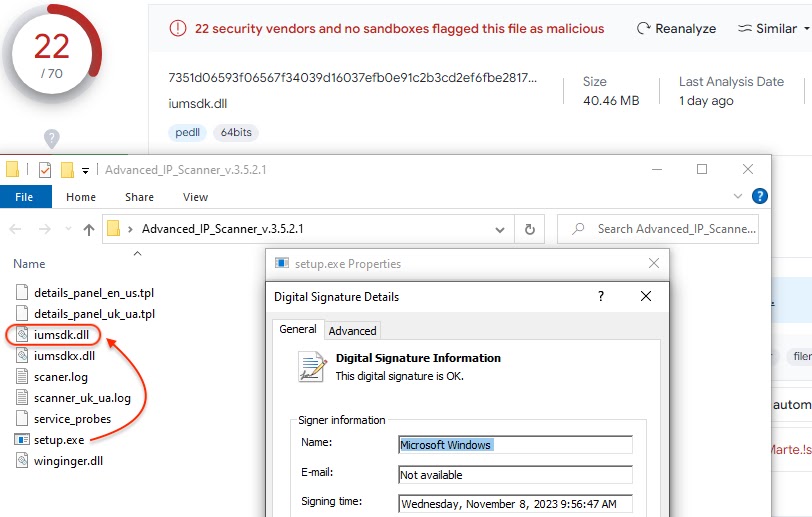
The fake software is signed using a codesigning certificate; once executed, it uses DLL side-loading via a signed executable to launch its payload, Jérôme Segura of Malwarebytes said.
The complex and convoluted Python scripts are designed to include potential targets in the attacker’s database for future actions. The misuse of online advertisements by malicious actors has been a long-standing concern since 2022.
Follow us on LinkedIn for the latest cybersecurity news, whitepapers, infographics, and more. Stay informed and up-to-date with the latest trends in cybersecurity.
Read the full article here

