Cybersecurity researchers have published the inner workings of a new wiper called Azov Ransomware that’s deliberately designed to corrupt data and “inflict impeccable damage” to compromised systems.
Distributed through another malware loader known as SmokeLoader, the malware has been described as an “effective, fast, and unfortunately unrecoverable data wiper,” by Israeli cybersecurity company Check Point. Its origins have yet to be determined.
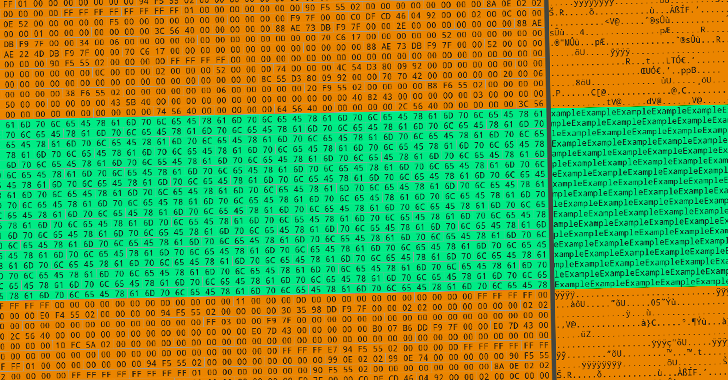
The wiper routine is set to overwrite a file’s contents in alternating 666-byte chunks with random noise, a technique referred to as intermittent encryption that’s being increasingly leveraged by ransomware operators to evade detection and encrypt victims’ files faster.
“One thing that sets Azov apart from your garden-variety ransomware is its modification of certain 64-bit executables to execute its own code,” threat researcher Jiří Vinopal said. “The modification of executables is done using polymorphic code, so as not to be potentially foiled by static signatures.”
Azov Ransomware also incorporates a logic bomb – a set of conditions that should be met before activating a malicious action – to detonate the execution of the wiping and backdooring functions at a predetermined time.
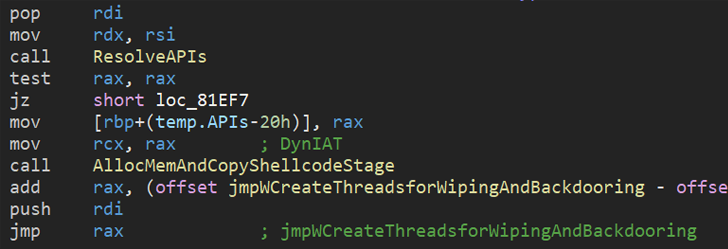
“Although the Azov sample was considered skidsware when first encountered […], when probed further one finds very advanced techniques — manually crafted assembly, injecting payloads into executables in order to backdoor them, and several anti-analysis tricks usually reserved for security textbooks or high-profile brand-name cybercrime tools,” Vinopal added.
The development comes amid a profusion of destructive wiper attacks since the start of the year. This includes WhisperGate, HermeticWiper, AcidRain, IsaacWiper, CaddyWiper, Industroyer2, DoubleZero, RURansom, and CryWiper.
Last week, security firm ESET disclosed another previously unseen wiper called Fantasy that’s spread using a supply chain attack targeting an Israeli software company to target customers in the diamond industry. The malware has been linked to a threat actor called Agrius.
Read the full article here