The Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the Federal Bureau of Investigation (FBI) and the Multi-State Information Sharing and Analysis Center (MS-ISAC), has released a comprehensive guide.
It aimed at assisting federal, state, local, tribal, and territorial government entities in responding to Distributed Denial-of-Service (DDoS) attacks.
Understanding the Threat Landscape
DDoS attacks originate from multiple sources and can be particularly challenging to trace and block.
The guide provides an in-depth overview of the DoS and DDoS landscapes, detailing attack types, motivations, and potential impacts on government operations.
It emphasizes the importance of planning for emerging DDoS trends and technologies to better defend against malicious activity.
CISA and FBI have recently released a comprehensive guide that provides technical details and best practices to respond effectively to Distributed Denial of Service (DDoS) attacks.
Free Webinar : Mitigating Vulnerability & 0-day Threats
Alert Fatigue that helps no one as security teams need to triage 100s of vulnerabilities.
:
- The problem of vulnerability fatigue today
- Difference between CVSS-specific vulnerability vs risk-based vulnerability
- Evaluating vulnerabilities based on the business impact/risk
- Automation to reduce alert fatigue and enhance security posture significantly
AcuRisQ, which helps you to quantify risk accurately:
DoS vs. DDoS: What’s the Difference?
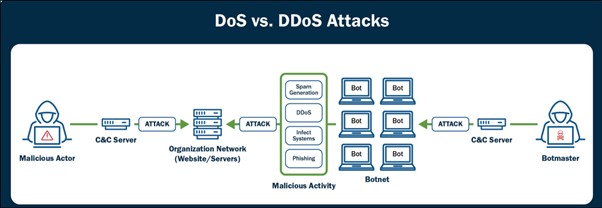
The guide clarifies the distinction between DoS and DDoS attacks.
A DoS attack typically involves a single source overwhelming a system with traffic, while a DDoS attack uses multiple sources, often coordinated through botnets, to amplify the disruption.
The distributed nature of DDoS attacks makes them more challenging to defend against.
CISA Cyber recently tweeted about the release of a guide by CISA and FBI that provides detailed information on how to respond to DDoS attacks
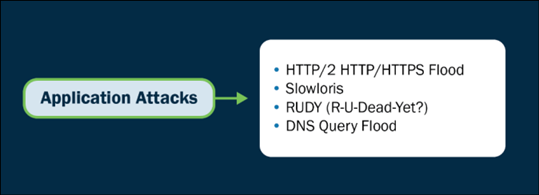
Categorizing DDoS Attacks
DDoS attacks are categorized into three main types:
- Volume-Based Attacks: These aim to consume bandwidth or system resources by overwhelming the target with massive traffic.
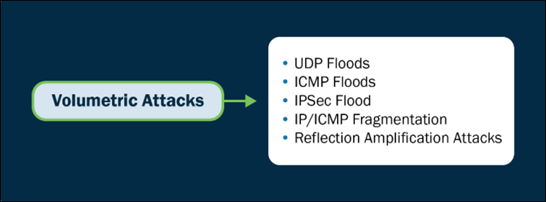
- Protocol-Based Attacks: These exploit network protocol vulnerabilities to degrade performance or cause malfunctions, often targeting Layers 3 and 4 of the OSI model.
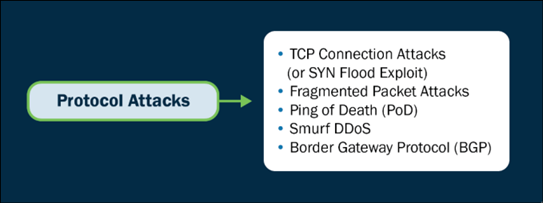
- Application Layer-Based Attacks: These attack specific applications or services, exploiting weaknesses to consume processing power or cause malfunctions. They focus on Layer 7 of the OSI model.
Proactive Steps Against DDoS Attacks
The guide outlines several proactive measures organizations can take to minimize the potential damage of a DDoS attack:
- Conducting risk assessments
- Implementing robust network monitoring
- Analyzing traffic to establish a baseline
- Integrating Captcha challenges
- Developing a comprehensive incident response plan
- Employing DDoS mitigation services
- Planning for bandwidth capacity
- Implementing load-balancing solutions
- Configuring firewalls and updating systems
- Ensuring redundancy and failover mechanisms
- Training employees on cybersecurity awareness
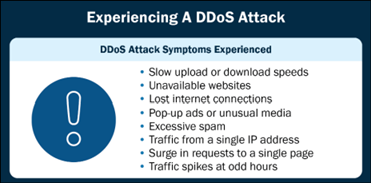
Identifying a DDoS Attack
Recognizing a DDoS attack can be challenging.
The guide lists symptoms such as website unavailability, network congestion, unusual traffic patterns, server crashes, high resource utilization, and communication disruptions as potential indicators of an ongoing attack.
Responding to a DDoS Incident
When an attack is identified, organizations are advised to:
- Activate their incident response plan
- Notify service providers
- Gather evidence
- Implement traffic filtering
- Enable DDoS mitigation services
- Scale up bandwidth and resources
- Utilize CDN services
- Maintain clear communication with stakeholders
- Learn from the attack to improve future responses
Recovery and Reporting
Post-attack, organizations should assess the impact, restore services, perform a post-incident analysis, implement remediation measures, review security controls, update incident response plans, educate employees, enhance network monitoring, engage with law enforcement, and maintain transparent communication with stakeholders.
The joint guide released by CISA, FBI, and MS-ISAC is a critical resource for government agencies and organizations.
It provides them with the necessary tools and knowledge to effectively respond to and recover from DDoS attacks, ensuring the resilience and security of their operations in the face of evolving cyber threats.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here