The Coper malware, a descendant of the Exobot malware family, was first distributed as a fake version of Bancolombia’s ‘Personas’ application.
Fast forwarding to 2022, the malware was discovered, and a lite version of the same malware was advertised on underground forums under the name “Octo Android botnet”.
However, the malware has been presently found to be offered as a malware-as-a-service in which customers are provided with access to a panel and builder used for executing the campaigns.
Moreover, the malware is capable of keylogging, interception of push notifications and SMS messages, as well as control over the infected device’s screen.
Android Malware-as-a-Service
According to the reports shared with Cyber Security News, the evolution of the malware started in 2021 when it targeted Colombian Android users using several tactics, including impersonation of legitimate banking applications and other applications to create trust with victims for installation.
Malware analysis can be fast and simple. Just let us show you the way to:
- Interact with malware safely
- Set up virtual machine in Linux and all Windows OS versions
- Work in a team
- Get detailed reports with maximum data
If you want to test all these features now with completely free access to the sandbox: ..
The malware also steals sensitive information such as passwords and login credentials by displaying fake screens or overlays and also utilizes VNC for remote access to affecting devices as a means of enhancing surveillance capabilities. Targets of this malware include countries like Portugal, Spain, Turkey, and the United States.
Malware Analysis
Initial C2 capabilities
Any social engineering techniques like phishing deliver the malware. Once the target has been compromised, the communication to the C2 is established and the payload (configuration file, parameters, and many others) is passed to the victim device.
The payload parameters include block_push_apps, desired_apps, domains_bot, keylogger_enabled, injects_list and many others.
Additionally, the smarts_ver configuration field is managed via a Table that contains further payload information such as inject type, inject ID, special injects, Gmail, pattern, and PIN.
Moreover, the malware also supports several injects such as Accessibility index, Fake pattern, Gmail fake, and URL inject.
Victim Registering and Filtering
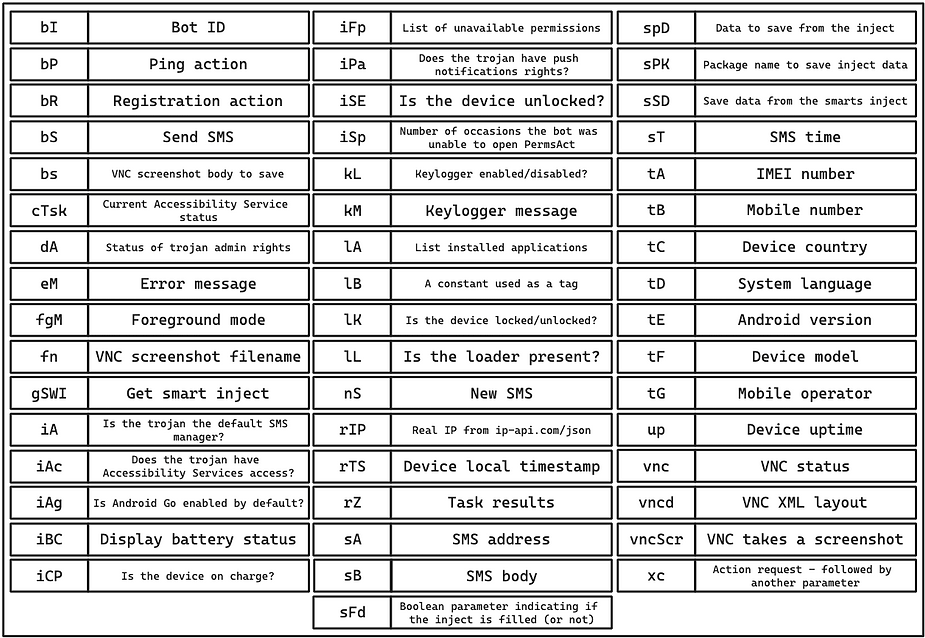
The affected victim device information such as the IMEI number, phone model, Android version, device uptime, etc., is collected and stored in an SQL database and registered on the C2 server.
Once the device is registered, the malware continues to send updates about the device to the C2 server daily. When every is set up appropriately, the threat actor can now control the device using additional commands.
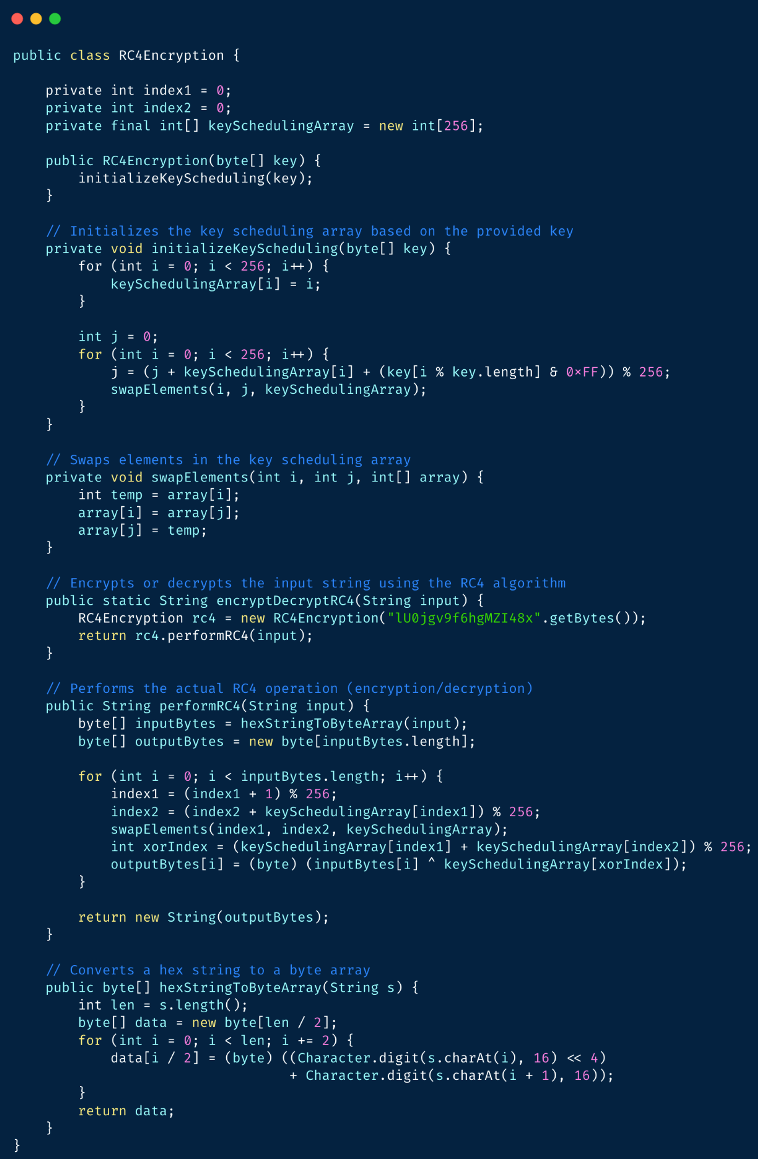
Encryption/Evading Detection
As part of the evasion technique, the malware is encrypted using a hardcoded RC4 key, and the traces of the malware are hidden using certain permissions like REQUEST_COMPANION_RUN_IN_BACKGROUND and REQUEST_COMPANION_USE_DATA_IN_BACKGROUND.
These permissions allow the malware to hide in the shadows without being detected.
Capabilities in Action
Analyzing the malware’s functionalities, the keylogging feature logs every keystroke made on the victim’s phone, and the keylogger status is also frequently verified to check if it is enabled.
The keylogging information is stored on a file within the device’s data directory.
However, the file is deleted after it has been fully read.
Injects
Injects are initially configured in the bot and can be later modified from the C2 panel.
Moreover, these inject can also be used to obtain an infected device’s screen password or PIN and enable remote access and management of the device.
VNC
VNC allows the threat actors to view and record the screen of the affected devices for capturing banking services or applications and websites of the threat actor’s interest.
This is an alternative that the threat actors can use apart from the other functionalities mentioned earlier.
SMS Message Interaction
This is the final capability of the malware that allows it to interact with the SMS messaging services enabling the malware to intercept, read, and send messages within the device.
However, just like every other capability, this feature also needs to be provided with the required permissions.
C2 Infrastructure Overview and Stats
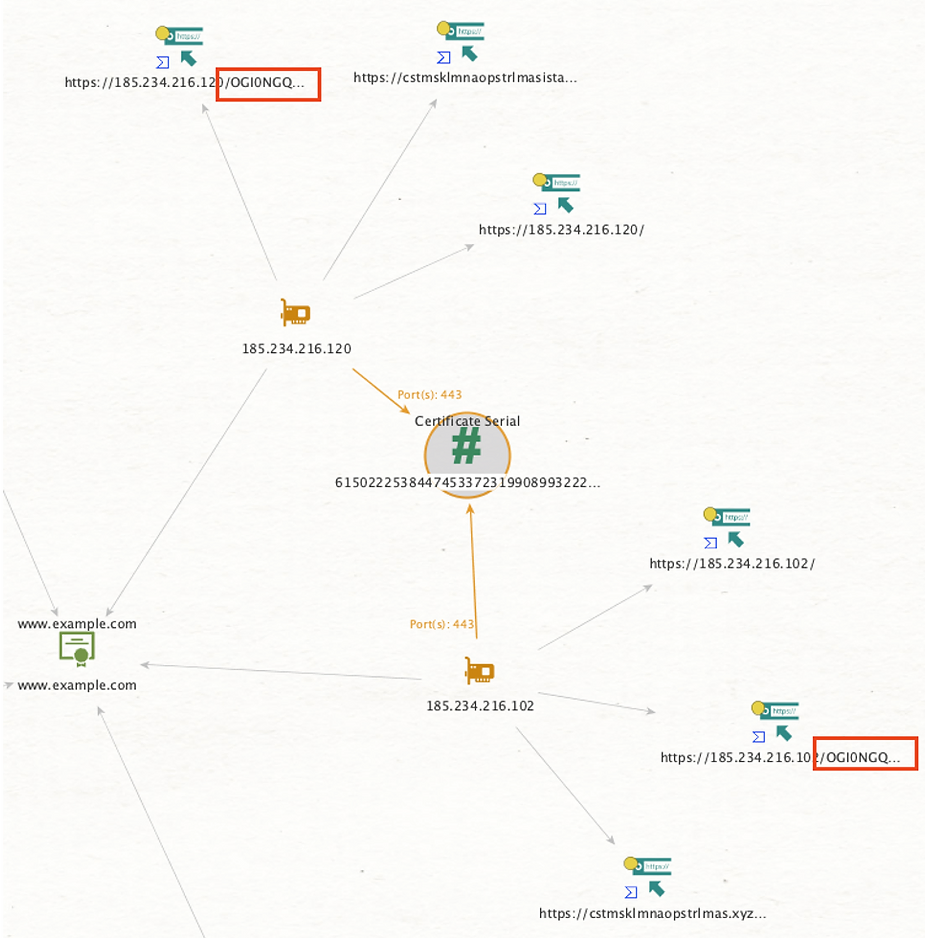
After several steps of decryption from an observed payload and an IP address using several tools such as Wireshark, Triage, and CyberChef, information about the C2 infrastructure has been obtained which stated that there were several levels of encryption between the communication with the C2 server.
One of the analyzed communications mentioned that the payload to one of the victim devices was impersonating the Facebook application, prompting the user to enable the Accessibility Service permissions required for the malware bot to operate fully.
Further analysis revealed that there were 84 other C2 server IPs all of which had similar X.509 certificates.
Additionally, there were also pieces of evidence that showed that the threat actors have been moving their infrastructure.
There were 45000 bots found, and nearly 700,000 SMS messages were intercepted by them.
Indicators of Compromise
- https://karmelinanoonethousandbaby[.]net/YzI4MGFhZjI2MmM5/
- https://185.198.69[.]111/NTBiZmM4ZDQ2MWY2/
- https://2.57.149[.]150/ZTIwNDEzZjM4YjYw/
- https://2istanbullu2586[.]xyz/ZTIwNDEzZjM4YjYw/
- https://83.97.73[.]195/MzZhMGJjZTJkOGI3/
- https://o3c31x4fqdw2[.]lt/MTU2OWE0NzJjNGY5/
- https://0n75w55jyk66[.]pw/MTU2OWE0NzJjNGY5/
- https://91.240.118[.]224/NjQyNDcyMjE3ZWU3/
- https://sanagerekkalmaz1453[.]shop/MTFiMzQ4NGQ2MWU4/
- https://185.122.204[.]122/MDViMDU3NDYwMTBm/
You can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware protection. All are incredibly harmful, can wreak havoc, and damage your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here