Cybersecurity researchers exposed new evasion techniques adopted by an advanced malware downloader called GuLoader.
CrowdStrike researchers d a detailed multiple evasion techniques implemented by an advanced malware downloader called GuLoader (aka CloudEyE).
GuLoader uses a polymorphic shellcode loader to avoid traditional security solutions, the experts mapped all embedded DJB2 hash values for every API used by the malicious code.
The malware uses an anti-analysis technique to avoid execution in virtualized environments.
“In dissecting GuLoader’s shellcode, CrowdStrike revealed a new anti-analysis technique meant to detect if the malware is running in a hostile environment by scanning the entire process memory for any Virtual Machine (VM)-related strings.” reads the analysis published by CrowdStrike.
“New redundant code injection mechanism means to ensure code execution by using inline assembly to bypass user mode hooks from security solutions.”
GuLoader first appeared on the threat landscape in 2019, it was used by threat actors to download multiple remote access trojans (RATs) such as AgentTesla, FormBook, Nanocore, NETWIRE and the Parallax RAT.
Early versions of GuLoader were distributed via spam messages using attachments containing the malicious executable. Recent variants were delivered via a Visual Basic Script (VBS) file.
“GuLoader also started employing advanced anti-analysis techniques to evade detection, such as anti-debug, anti-sandbox, anti-VM and anti-detection to make analysis difficult.” reads the analysis.
A recent GuLoader variant analyzed by the experts exhibits a multistage deployment:
- The first stage uses a VBS dropper file to drop a second-stage packed payload into a registry key. It then uses a PowerShell script to execute and unpack the second stage payload from the registry key within memory.
- The second stage payload performs all anti-analysis routines (described below), creates a Windows process (e.g., an ieinstal.exe) and injects the same shellcode into the new process.
- The third stage reimplements all the anti-analysis techniques, downloads the final payload from a remote server and executes it on the victim’s machine.
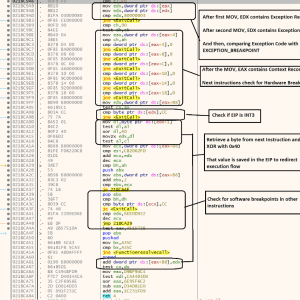
The malware implements anti-debugging and anti-disassembling checks to detect the presence of breakpoints used for the analysis of code.
The researchers also noticed the use of a redundant code injection mechanism to avoid NTDLL.dll hooks used by antivirus and EDR solutions to detect malicious activities.
“It then maps that section via NtMapViewofSection on the suspended process.” continues the analysis. “If this injection technique fails, it uses the following redundancy method:
a. NtAllocateVirtualMemory by invoking the inline assembly instructions (without calling ntdll.dll, to bypass AV/EDR User Mode hooks) of that function, using the following assembly stub:
mov eax,18
mov edx,ntdll.77178850
call edx
ret 18 It uses NtWriteProcessMemory to copy the same shellcode onto that virtually allocated address. It uses NtWriteProcessMemory to copy the same shellcode onto that virtually allocated address.”
Experts pointed out that GuLoader remains a dangerous threat that constantly evolves, they also shared Indicators of Compromise for the latest variant of the downloader.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, GuLoader)
Share On
Read the full article here