A recent phishing campaign targeting Latin America utilized emails with ZIP attachments containing an HTML file disguised as an invoice using free, temporary email addresses with the domain “temporary.link” and spoofing the User-Agent field in the header to indicate use of Roundcube Webmail, a platform that phishers frequently abuse, aiming to trick recipients into downloading malware.
A potentially malicious URL is identified within an HTML file, which, accessed directly, leads to a non-functional page, indicating the URL resolves to IP address 89.116.32.138.
Phishing Scheme With Expired Domains
TrustWave investigation reveals the domain is young (approximately one year old) and utilizes Cloudflare nameservers. Some registrant contact information for this domain traces back to Mexico, which raises suspicion about the URL’s legitimacy.


Attackers are targeting users in Mexico with a phishing scheme, and by accessing a specific URL with a Mexican IP, victims are redirected to a page requesting human verification.
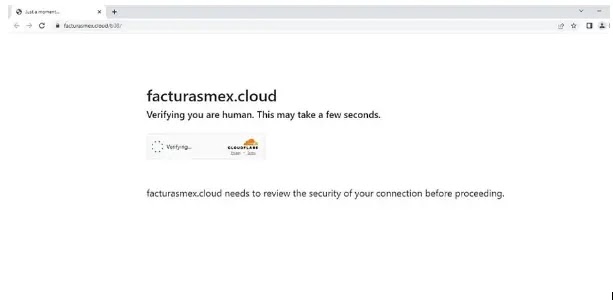
The verification step leads to the download of a malicious RAR archive, which contains a PowerShell script designed to gather information from the victim’s machine, including the computer’s name, operating system, and antivirus presence.
The script also contains encoded URLs that, when decoded, initiate further malicious actions, potentially including downloading additional malware.

A malicious website encoded with a base64 string attempts to identify the user’s country through a URL (hxxp[://]86[.]38[.]217[.]167/ps/index[.]PHP), which might be part of a larger campaign similar to previous “Horabot” campaigns.
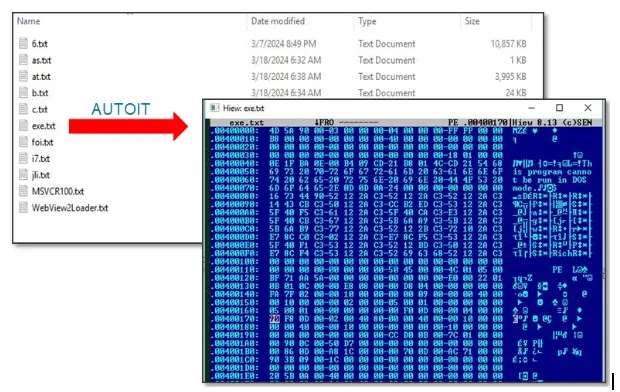
Another encoded string leads to a malicious URL (hxxps[://]www[.]dropbox[.]com/scl/fi/k6hxua7lwt1qcgmqou6q3/m[.]zip?rlkey=7wu6x4pfvbt64atx11uqpk34l&dl=1) that downloads a ZIP archive containing suspicious files, including a newly created executable AutoIt file, suggesting potential malicious activity.
Phishing campaigns are employing increasingly sophisticated techniques to bypass detection, which include compressed attachments, obfuscated code, PowerShell scripts, and newly created domains with geo-targeted content.
The techniques make it difficult to identify malicious emails, especially those that contain attachments or links disguised as inaccessible or suspended pages.
According to TrustWave, some IoCs identified in such campaigns are: hxxps://facturasmex.cloud, hxxps://facturas.co.in/index.php?va, hxxp://ad2.gotdns.ch/22/22, hxxp://86.38.217.167/ps/index.php. Users should be cautious of emails with these characteristics and refrain from opening attachments or clicking on links.
Secure your emails in a heartbeat! Take Trustifi free 30-second assessment and get matched with your ideal email security vendor - Try Here
Read the full article here

