Race conditions arise when there is no insufficient synchronization with a shared resource allowing multiple threads to access it simultaneously.
The use of synchronization primitives such as mutexes, spinlock, etc. prevents these race conditions,
However, researchers have discovered a new race condition called “GhostRace ” which bypasses these synchronization primitives on speculatively executed code paths and performs a race condition on critical regions.
Additionally, these race conditions focussed on Speculative Concurrent Use-After-Free (SCUAF) conditions alongside 1283 potentially exploitable vulnerabilities present in the Linux Kernel.
GhostRace Attack
According to the reports shared with Cyber Security News, GhostRace is the first systematic analysis of Speculative Race Conditions (SRCs), a new class of speculative execution vulnerabilities that affect all common synchronization primitives.
Mitigating Vulnerability & 0-day Threats
Alert Fatigue that helps no one as security teams need to triage 100s of vulnerabilities.
:
- The problem of vulnerability fatigue today
- Difference between CVSS-specific vulnerability vs risk-based vulnerability
- Evaluating vulnerabilities based on the business impact/risk
- Automation to reduce alert fatigue and enhance security posture significantly
AcuRisQ, that helps you to quantify risk accurately:
However, threat actors can exploit these SRCs which can be elevated into race conditions which can result in disclosing victim data to the attacker.
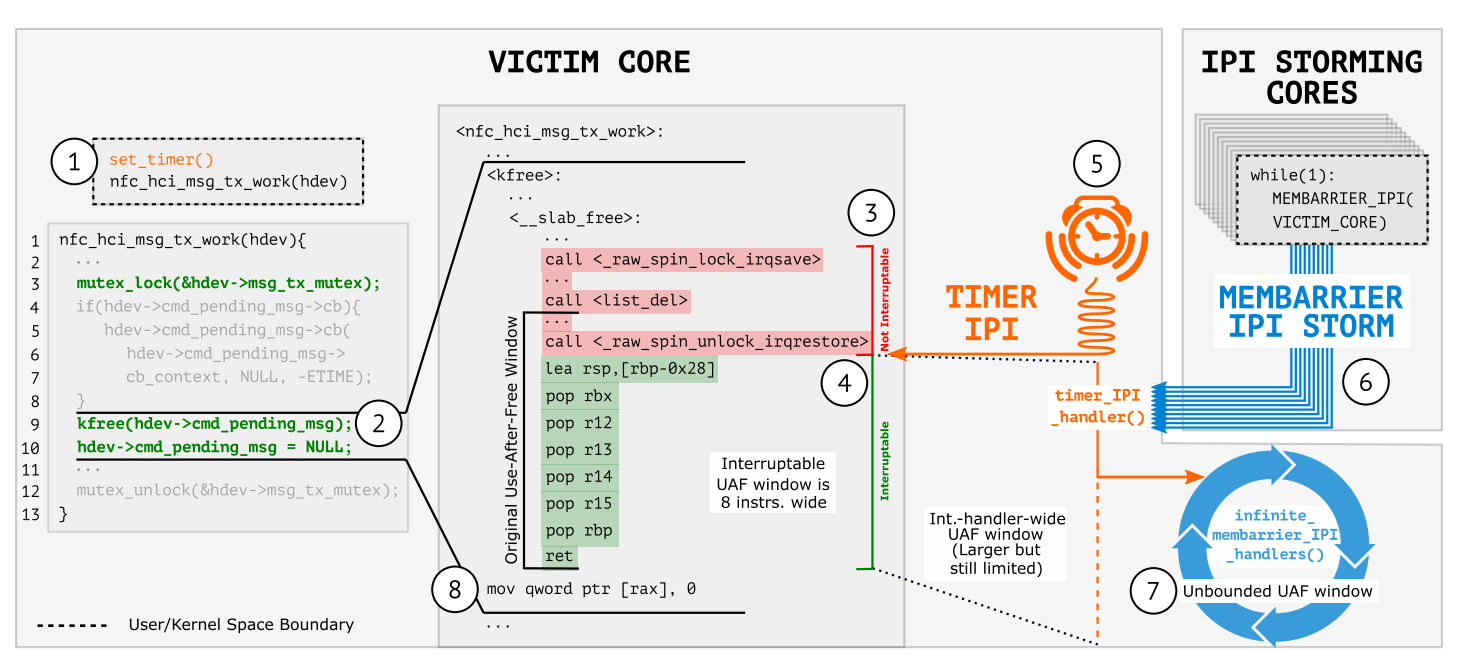
As for the attack surface, new techniques have been discovered to exploit the SCUAF that is currently in practice. These techniques include the challenges of Spectre and architecture race conditions.
The original exploitable depends on the controlling and stretching of the race window which fits the exploits.
However, there are limitations as the architectural race conditions can only be done with a single iteration of the primitive, and hence there will only be one race window.
The Spectre exploit requires thousands or millions of iterations to scan the memory to find a secret to leak.
GhostRace Attacks
The main goal of this GhostRace attack is to disclose the arbitrary kernel data by exploiting the speculative race condition.
This new technique of exploitation is capable of surgically interrupting the victim thread at the perfect time and creating an outbound window.
This makes the SCUAF attacks much more reliable and realistic.
Moreover, the researchers have also released a SCUAF gadget scanner, which was utilized to find more than 1200+ vulnerabilities.
In addition, a proof-of-concept has also been released which could be used to hijack the control flow to disclose gadgets in the Linux Kernel. An unprivileged threat actor can exploit this Linux kernel and leak arbitrary kernel memory at the rate of 12 KB/s.
With Perimeter81 malware protection, you can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits. All are incredibly harmful and can wreak havoc on your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here

