Threat actors use keyloggers to capture sensitive information by recording keystrokes on infected devices, as covert techniques and tactics allow them to steal valuable information without the victim’s knowledge.
Governments or threat actors can deploy Keyloggers as espionage tools to gather intelligence or monitor their targets.
Recently, the cybersecurity researchers at Splunk Threat Research Team unveiled SnakeKeylogger attacks, techniques, and tactics.
SnakeKeylogger Attack Techniques
Snake Keylogger steals credentials and logs keystrokes. It was developed in .NET and captures screenshots, clipboard data, browser credentials, and system information.
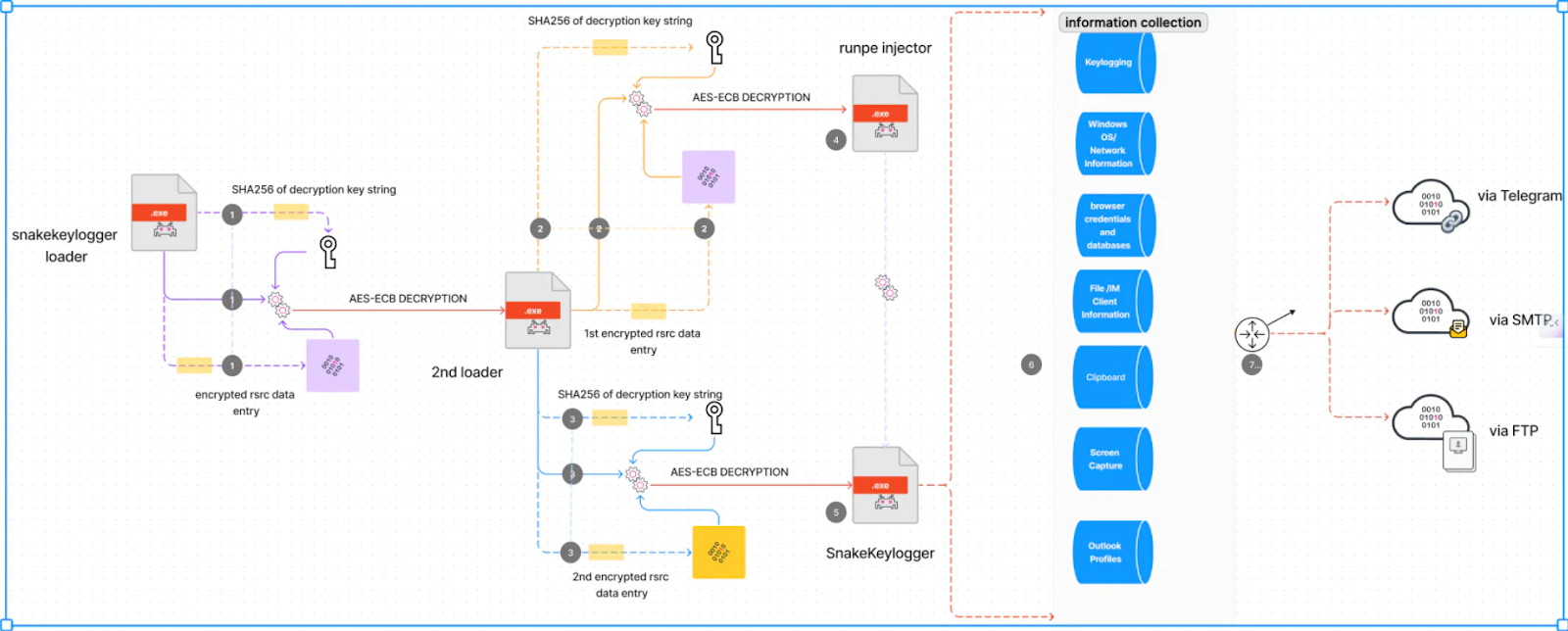
It uses FTP, email, and Telegram for data exfiltration. Diverse C2 infrastructure enhances the operational effectiveness against traditional defenses.
Snake Keylogger spreads through phishing and obfuscates code with cryptors/loaders to evade sandboxes. This loader parses .RSRC entry name computes the SHA256 hash of the key string for AES-ECB decryption of encrypted .RSRC payload.
While its complex tactics challenge the analysis. Decrypted data has another loader with two AES-ECB encrypted .RSRC entries using different keys.
Decrypting these reveals a RUNPE injector and the actual Snake Keylogger payload.
The Snake Keylogger gathers system information, such as OS version, RAM, and HDD details, and formats data before sending it to the C2 server.
It queries reallygeoip[.]org to locate the host machine geographically, extracting city, country, latitude, longitude, region, and timezone.
This data boosts situational awareness for targeted attacks.
It uses registry run keys for persistence and includes a ‘Kill Switch’ that terminates if the build date is earlier than the current date.
This tactic is an anti-sandbox method that helps to evade security detection.
Snake Keylogger often uses Crypter or loaders, requiring reverse engineering to bypass its date check, adding complexity for
It prompts user choices with choice.exe, using “/T” for the delay before cleanup. It terminates security tools’ processes to evade detection and maintains a list of sandbox IPs.
Snake Keylogger checks for specific IP addresses before executing the payload. It exfiltrates the system, network, and browser credentials to C2 if clear.
This environment detection evades the security checks. It targets major browsers and email/file clients for credentials and credit cards.
Harvests Outlook profiles from the registry for usernames/passwords. Steals clipboard data like passwords, cards, and text for data theft.
This keylogger periodically captures screenshots such as “Screenshot.jpg” in the user’s Documents folder for visual data theft.
Its core capability is covert keystroke logging to harvest credentials and type sensitive information, reads Splunk report.
It initiates by contacting the C2 server, verifying activity if the response contains “#$0#”. Like Agent Tesla, it uses FTP, email, and Telegram C2 channels specified in the config to exfiltrate data.
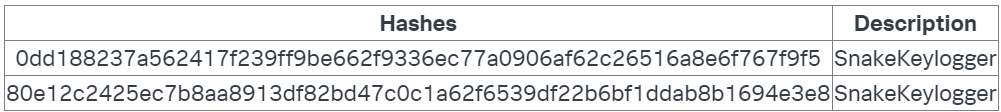
IOCs
With Perimeter81 malware protection, you can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits. All are incredibly harmful and can wreak havoc on your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here