A new tool has surfaced on the Dark Web, signaling a shift in cybercriminals’ methods for gaining unauthorized remote access to corporate networks.
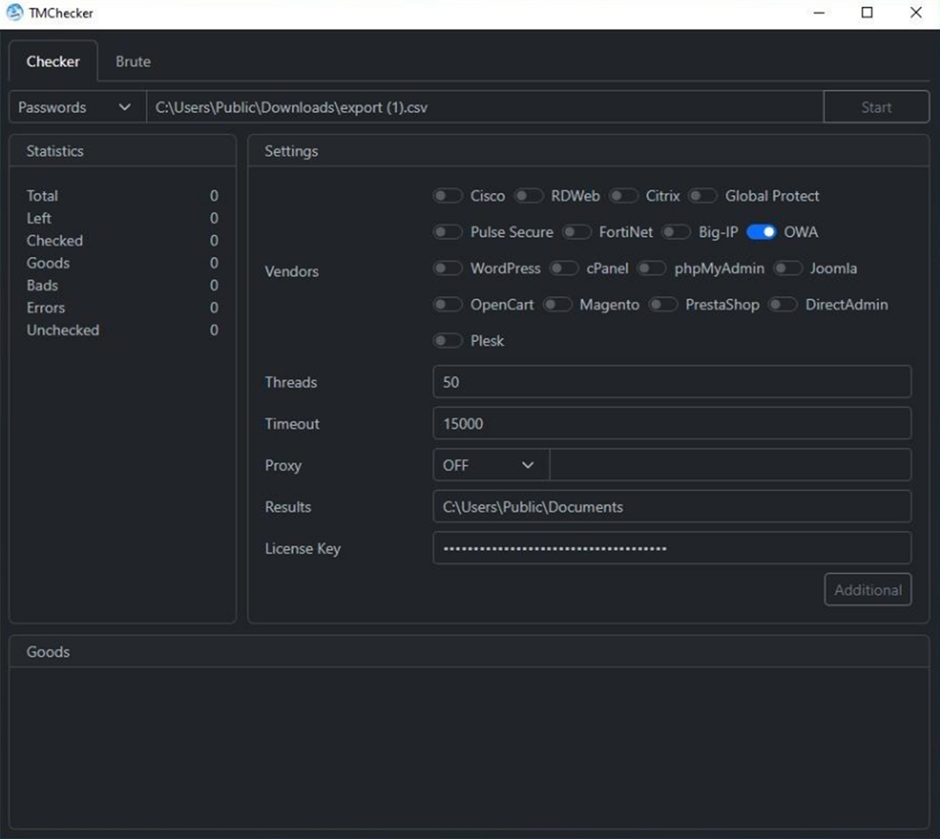
TMChecker, a tool recently identified by Security, is designed to attack remote-access services and popular e-commerce applications.
It combines corporate access login checking capabilities with a brute-force attack kit.
Developed by a threat actor known as “M762” on the XSS cybercrime forum, TMChecker is available on a monthly subscription basis for $200.
This tool is a step ahead of its counterparts like “ParanoidChecker,” targeting corporate remote access gateways, often the primary intrusion vectors for ransomware infections and other high-level attacks.
According to a report by Security, TMChecker supports 17 different services, including various VPN solutions, enterprise mail servers, database management tools, and e-commerce platforms.
Incident in Ecuador: A Case Study
A notable incident involving TMChecker was targeting an email server of a government organization in Ecuador (gob. ec).
This event underscores the tool’s effectiveness in compromising valid credentials to corporate VPN and email accounts, which can be used by ransomware operators and initial access brokers (IABs).
M762’s Telegram Channel: A Hub for Cybercriminals
The black-hat developer behind TMChecker, M762, operates a Telegram channel with over 3,270 subscribers.
While it’s unclear how many of these subscribers are active customers, the channel’s following provides insight into the profitability of this adversarial Software-as-a-Service (SaaS) model.
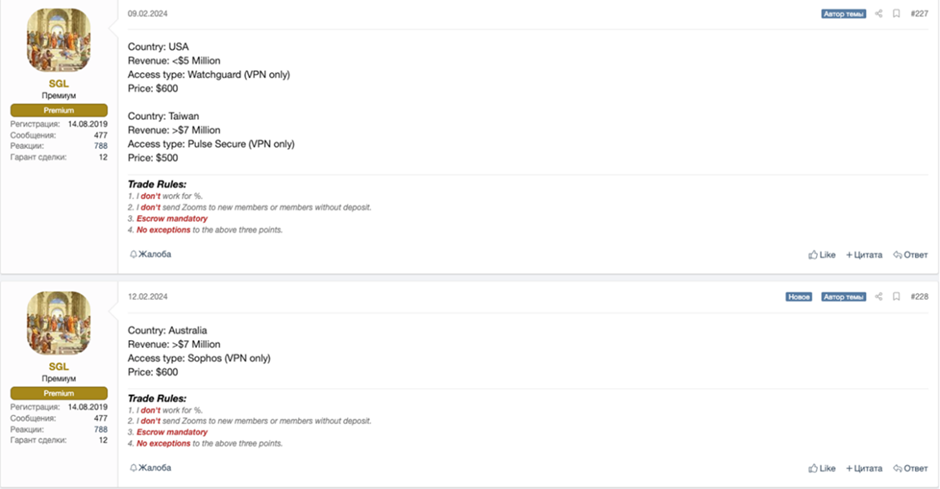
TMChecker’s extensive targets range from VPN gateways and hosting administration panels to e-commerce engines like Magento and PrestaShop.
This broad targeting spectrum indicates the tool’s potential to compromise various systems, making it a versatile asset for cybercriminals.
Significance: The Rise of Human-Operated Ransomware Attacks
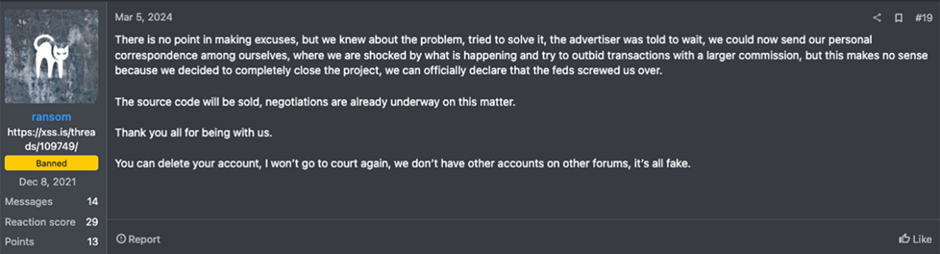
The emergence of TMChecker aligns with the increase in human-operated ransomware attacks, as reported by Microsoft.
These attacks involve the active abuse of remote monitoring and management tools, allowing hackers to leave behind less evidence compared to automated attacks.
The trend is expected to continue in 2024, with ransomware actors seeking to maximize returns by working for multiple gangs.
The advent of TMChecker represents a significant threat to organizations, particularly in the context of corporate mergers and acquisitions (M&A).
With the tool’s ability to lower the barriers to entry for cybercriminals, the private sector must bolster its cyber-due diligence processes.
Resecurity’s RISKTM platform offers a solution by providing advanced cyber threat intelligence capabilities to help corporate acquirers mitigate the risk of post-acquisition breaches.
As cybercriminals continue to refine their tooling for remote access compromise, organizations must remain vigilant and proactive in their cybersecurity efforts to protect against these evolving threats.
With Perimeter81 malware protection, you can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits. All are incredibly harmful and can wreak havoc on your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.
Read the full article here

