Zloader, also known as Terdot, DELoader, or Silent Night, is a modular trojan that reappeared after nearly two years of absence but with significant enhancements to the loader module.
Zloader has returned with upgrades to RSA encryption, an updated DGA, and more effective obfuscation techniques such as more junk code, hashing API imports, and string encryption to prevent malware analysis.
The malicious behavior of Zloader, which originated from the leaked Zeus source code, dates back to at least August 2015. It was made public in 2016 during a targeted effort against German banks.
Open Suspicious Files & Links in the ANY RUN Sandbox Safely; Try All Features for Free. Understand malware behavior, collect IOCs, and easily map malicious actions to TTPs — all in our interactive sandbox.
Zloader’s development continued rapidly, culminating in the creation of version 2.0.0.0 in September 2021. The threat actors utilizing Zloader switched from committing financial fraud to ransomware, similar to Qakbot.
Security researchers carried out a takedown operation in April 2022 to remove the botnet, which resulted in an extended period of inactivity.
In September 2023, Zloader reappeared with a new version that seemed to have begun development.
Zloader’s new updates to RSA Encryption
Asymmetric encryption, such as RSA, uses two distinct but connected keys. RSA cryptography allows for message encryption using both the public and private keys. A message can be decrypted using the opposite key which was used to encrypt it.
According to ThreatLabz researchers, Zloader currently communicates with its C2 server via HTTP POST requests. Nevertheless, the Zeus “visual encryption” algorithms and 1,024-bit RSA with RC4 are already being used for network encryption.
Zloader employs the unique Zeus BinStorage format, in which the RSA-encrypted RC4 key (32 random bytes) makes up the first 128 bytes, and the RC4 key and visual encryption encrypt the remaining bytes.
The information stored is represented by an ID integer value in the Zeus BinStorage structure, which is followed by the length and data.
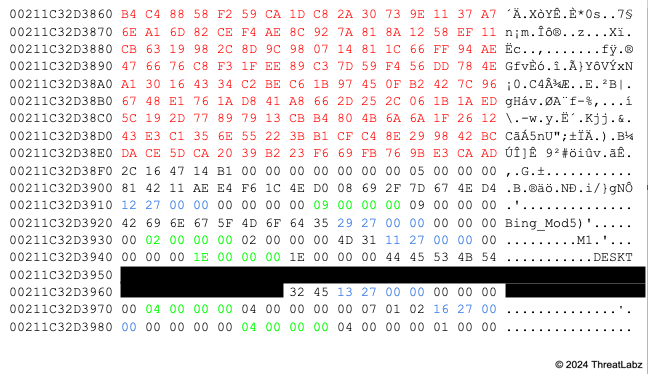
The Zloader static configuration is still encrypted using RC4 and a hardcoded alphanumeric key, but the structure differs slightly. The botnet ID, campaign name, and command-and-control servers (C2s) are all set at fixed offsets, along with an RSA public key that replaces an old RC4 key used for network encryption.
Researchers have discovered fifteen distinct Zloader variants, and they are all using the same RSA public key, which suggests that just one threat actor is presently using the malware.
Final Words
The loader module of Zloader was significantly modified in the latest version, which also updated the domain generation process and introduced RSA encryption. This was the first time that Zloader was compiled for 64-bit Windows operating systems.
To hinder malware investigation, Zloader persists in employing string encryption, API import hashing, and junk code for obfuscation.
Try Kelltron’s cost-effective penetration testing services to evaluate digital systems security. Free demo available.
Read the full article here