Threat actors using the DLL Hijacking technique for persistence have been the order of the day and have been utilized in several attacks.
This attack method allows bypassing the privilege requirement for executing certain malicious codes on the affected system.
However, a new DLL Hijacking method has been discovered to be used by the threat actors, which uses the trusted WinSxS folder and exploits it by the use of the traditional DLL Search Order Hijacking technique. This new method has been compatible with both Windows 10 and 11.
Windows Security Using DLL
According to Security Joe’s report, this approach allows for improvement and simplification of the DLL Search Order Hijacking method.
The behavior was possible due to the native behavior of Windows and the functionalities it offers for developers and end-users.
This new DLL hijacking method has a low probability of detection since the malicious code operates within the memory space of a trusted binary located in the Windows folder WinSxS.
Threat actors using the DLL Hijacking technique for persistence have been the order of the day and have been utilized in several attacks.
This attack method allows bypassing the privilege requirement for executing certain malicious codes on the affected system.
However, a new DLL Hijacking method has been discovered to be used by the threat actors, which uses the trusted WinSxS folder and exploits it by the use of the traditional DLL Search Order Hijacking technique. This new method has been compatible with both Windows 10 and 11.
DLL Search Order Hijacking
According to the reports shared with Cyber Security News, this approach allows for improvement and simplification of the DLL Search Order Hijacking method.
The behavior was possible due to the native behavior of Windows and the functionalities it offers for developers and end-users.
This new DLL hijacking method has a low probability of detection since the malicious code operates within the memory space of a trusted binary located in the Windows folder WinSxS.
The traditional DLL Search Order Hijacking method takes advantage of the applications that do not specify the full path to the file (EXE/DLL) they require.
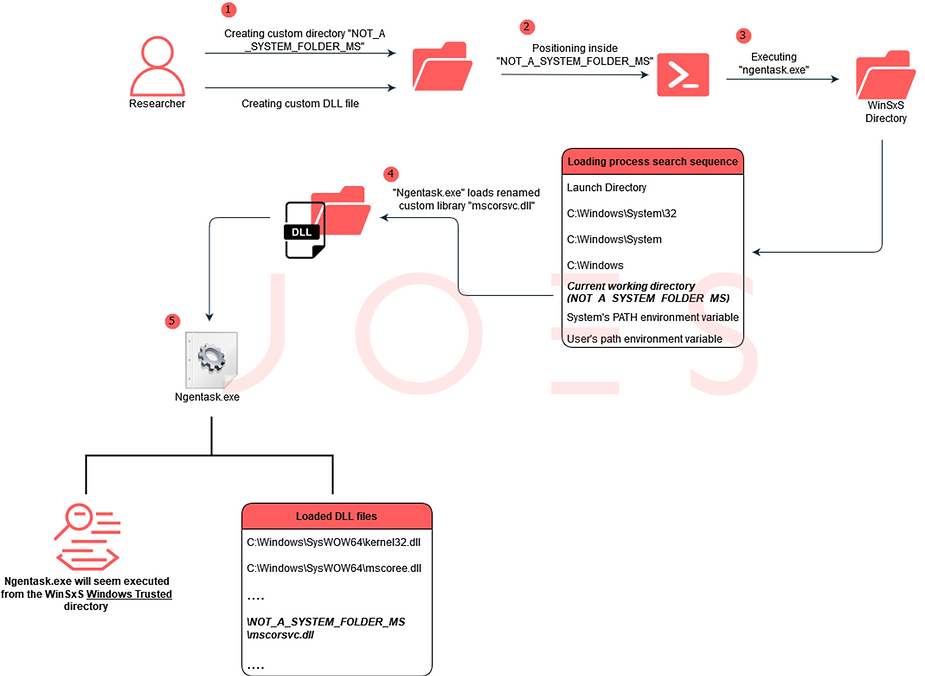
The only difference between the traditional and the new DLL hijacking technique is the targeting of files inside the WinSxS folder. The application DLLs residing inside the WinSxS folder have elevated privileges that can be utilized for malicious purposes.
The WinSxS (Windows Side by Side) folder is primarily used for storing various versions of important system files side by side, additionally as a critical component to maintain and recover the Windows Operating system located in the C:WindowsWinSxS.
To reveal the hidden secret, the original exploitation process was to place a custom malicious DLL into the designated directory, which closely resembles the name of the legitimate targeted DLL.
Furthermore, a complete report has been published that provides detailed information about the proof of concept, exploitation, and other information.
List of Vulnerable Executables in WinSxS folder
| Process Name | Loaded Resource |
| Conhost.exe | ClipUp.exe |
| Conhost.exe | ipconfig.exe |
| Conhost.exe | route.exe |
| Conhost.exe | mcbuilder.exe |
| Forfiles.exe | cmd.exe |
| Iediagcmd.exe | ipconfig.exe |
| Stordiag.exe | Systeminfo.exe |
| Aspnet_wp.exe | webengine.dll |
| Aspnet_wp.exe | webengine4.dll |
| Aspnet_regiis.exe | webengine4.dll |
| Aspnet_state.exe | webengine4.dll |
| Csc.exe | VCRUNTIME140_1_CLR0400.dll |
| Cvtres.exe | VCRUNTIME140_1_CLR0400.dll |
| Ilasm.exe | fusion.dll |
| Ilasm.exe | VCRUNTIME140_1_CLR0400.dll |
| Ngentask.exe | mscorsvc.dll |
| Ngen.exe | VCRUNTIME140_1_CLR0400.dll |
| NisSrv.exe | mpclient.dll |
Read the full article here

