IT admins can be considered culpable for weak password use if they fail to enforce strong password policies or neglect proper security measures.
Their responsibility includes setting and maintaining robust password standards, implementing multi-factor authentication, and educating users about password security.
Failure to do so can contribute to weak password practices and compromise system security, making IT admins partially responsible for any resulting vulnerabilities or breaches.
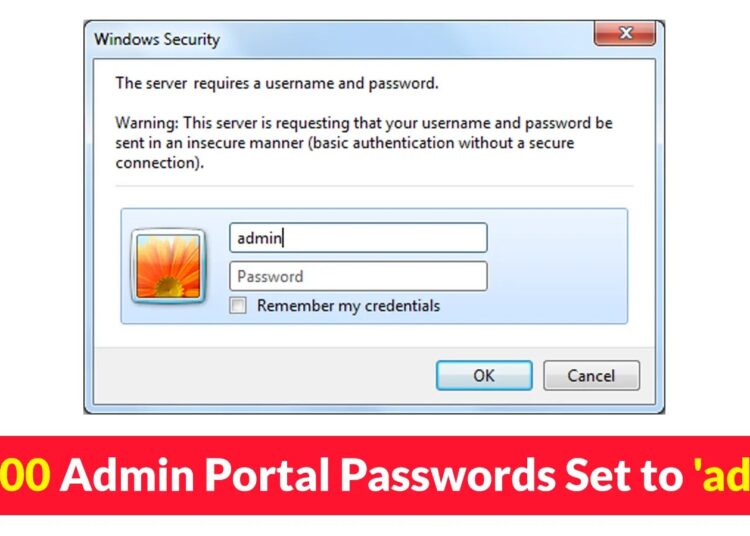
Outpost24’s analysis of 1.8 million passwords reveals ‘admin’ as the top choice, with over 40,000 occurrences, highlighting the persistence of default passwords.
Implementing AI-Powered Email security solutions “Trustifi” can secure your business from today’s most dangerous email threats, such as Email Tracking, Blocking, Modifying, Phishing, Account Take Over, Business Email Compromise, Malware & Ransomware
Default Passwords
Default passwords are also commonly accepted, according to Outpost24’s Threat Compass data, a solution that identifies compromised credentials for early threat mitigation.
Default passwords, like ‘admin’ or ‘password,’ are predefined and commonly known. They pose a significant security risk, are easy entry points for attackers, and have been prohibited by recent legislation.
However, based on data from credential-stealing malware reveals that many of these passwords could be easily guessed in unsophisticated attacks.
Top 20 Administrator Passwords
Researchers identified administrator passwords from a dataset of 1.8 million passwords collected in 2023.
Here are the top 20 administrator passwords as detected by Outpost24’s Threat Compass:-
- admin
- 123456
- 12345678
- 1234
- Password
- 123
- 12345
- admin123
- 123456789
- adminisp
- demo
- root
- 123123
- admin@123
- 123456aA@
- 01031974
- Admin@123
- 111111
- admin1234
- admin1
Technical analysis
Malware delivery methods vary, from phishing campaigns to specialized tactics. Organized groups like Traffers now use methods such as YouTube videos and Google ads to spread malware through deceptive content, targeting administrators with fake IT tools.
This malware can quietly collect personal data, including:-
- Login information
- Web browsers data
- FTP clients data
- Mail client account data
- Wallet files
Encryption can be bypassed in certain applications, like Google Chrome, allowing malware to request decryption of stored passwords.
These stolen passwords may end up in a marketplace for sale to attackers for several illicit purposes.
To safeguard passwords and critical business data, there are two key steps:-
- Enhancing password security with best practices
- Preventing malware infections
Recommendations
Here below we have mentioned all the recommendations below:-
- Stay safe with modern endpoint defense and antivirus solutions.
- Turn off browser password storage to protect against malware access.
- Make sure to confirm the correct site after clicking ads or links.
- Always remain vigilant, spotting domain typos and suspicious website signs.
- Do not use cracked software or applications.
- Reduce targeted attack risk with secure credentials.
Protect yourself from vulnerabilities using Patch Manager Plus to patch over 850 third-party applications quickly. Take advantage of the free trial to ensure 100% security.
Read the full article here