VirusTotal has introduced a Crowdsourced YARA Hub to overcome this hurdle, letting users find and filter existing rules, track a new rule, and export rules to LiveHunt or Retrohunt with a Single Click.
YARA (Yet Another Ridiculous Acronym) rules are malware detection patterns that can help strategize a targeted attack or a threat. VirusTotal is one of the largest platforms of Threat Intelligence utilized by security researchers.
VirusTotal offers both Livehunt (Streaming of files analyzed by VirusTotal and get notified when there is a match) and Retrohunt (scanning up to 12 months-old files sent to VirusTotal by user-created YARA rules).
VirusTotal has several contributors worldwide who submit various YARA rules that can identify and classify samples. Due to the increasingly large crowdsourcing of rules, Finding and keeping track of all the rules is challenging.

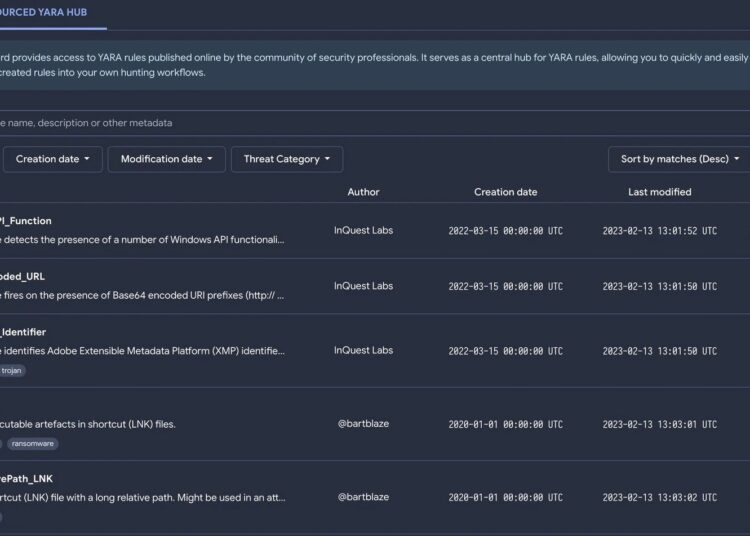
YARA Hub does not list private Livehunt or Retrohunt rulesets. Instead, it lists all the community YARA rules in the context of files currently being processed by VirusTotal. The YARA hub is found under “Livehunt” in VirusTotal.

Users can use this repository of YARA rules for searching different rules with multiple filters like Author, Number of matches, and threat category. In addition to this, there are also filters for the name, description, and metadata of the YARA rule.
According to the Virustotal report, If a user wants to find all rules related to “ransomware”, Users can rely upon this YARA hub if they are monitoring or creating a rule for campaigns or a threat actor that will be on top of fresh rules when there is a hit.
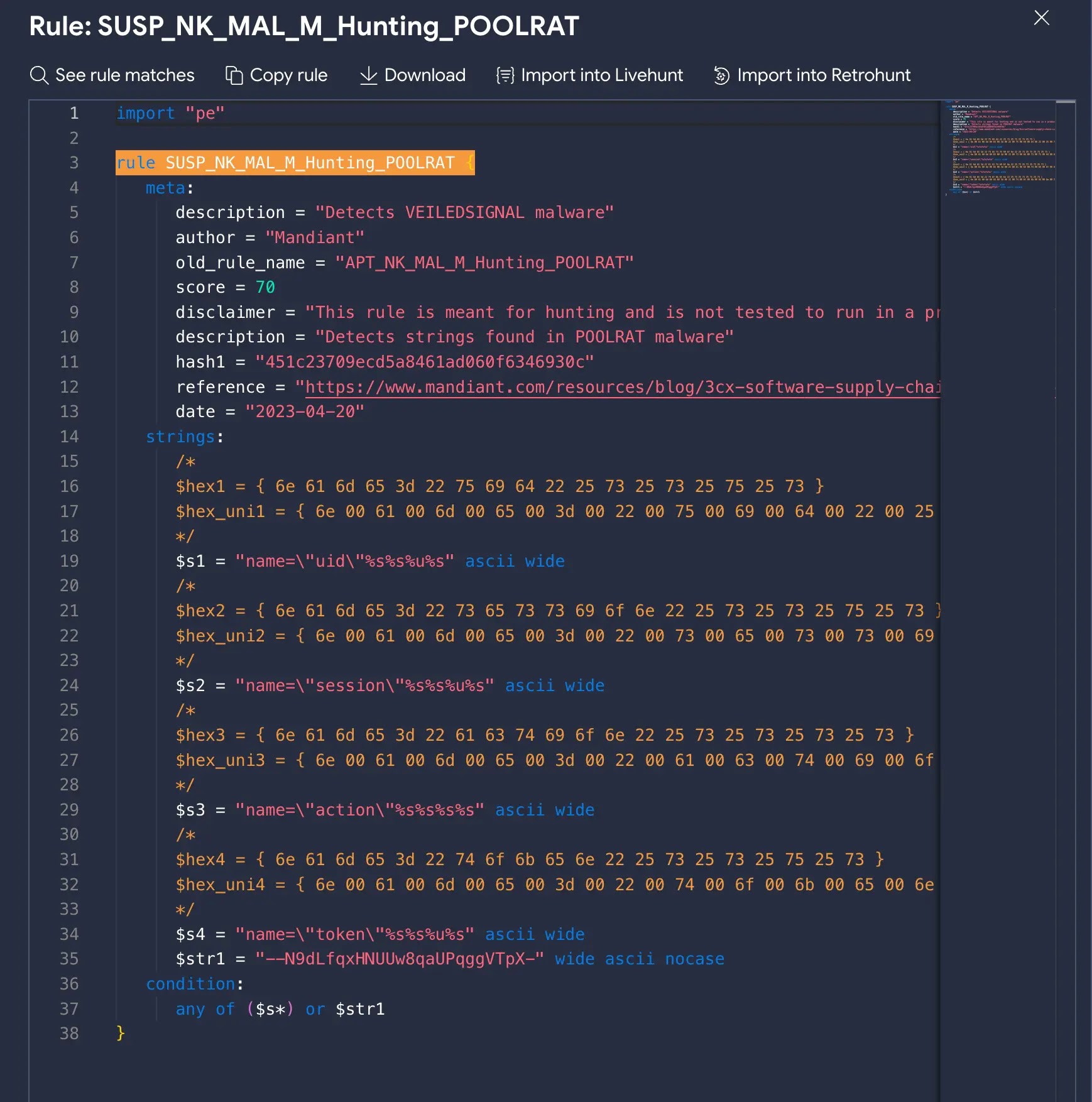
The download and export of the rule can be used for seeing it in action inside the environment through EDR or any other forensic investigation tools.
The additional visualization of the total number of matches also helps to understand the popularity of any rule and its impact during investigations.
Along with these features, the Hub permits users to pipeline files into VirusTotal and import rules inside Livehunt and Retrohunt.
Building Your Malware Defense Strategy – Download Free E-Book

Read the full article here