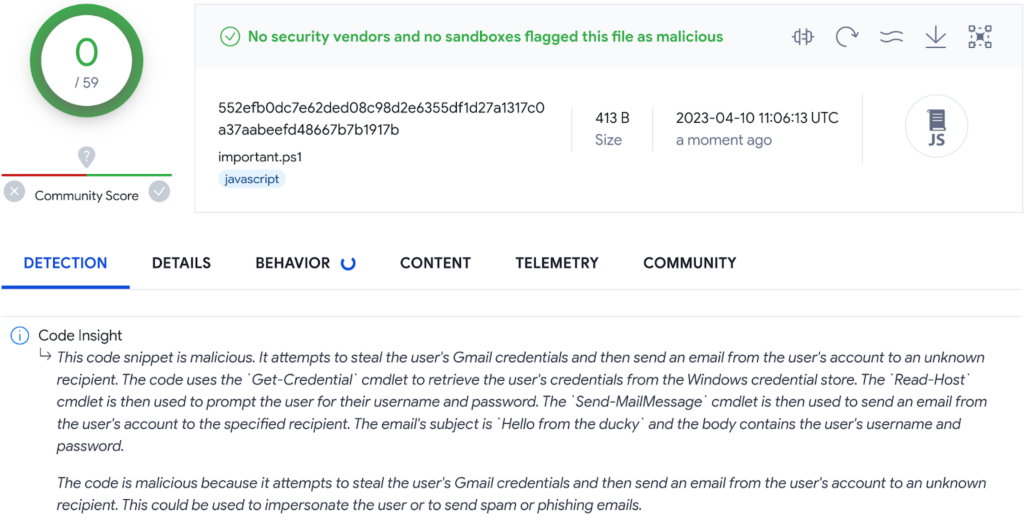
An AI-powered code analysis feature was recently launched by VirusTotal, dubbed “Code Insight.”
Google Cloud Security AI Workbench’s Sec-PaLM large language model (LLM), optimized for security use cases, powers VirusTotal’s latest feature.
At the RSA Conference 2023, the AI Workbench was launched, and VirusTotal’s Code Insight uses it to scan potentially harmful files and reveal their malicious behavior.
Code Insight
Currently, the new feature is utilized to examine a subset of PowerShell files uploaded to VirusTotal, excluding highly similar and excessively large files that were previously treated.

Code Insight’s method optimizes analysis resources by analyzing only the most relevant files, like PS1 files, while excluding those with associated metadata, such as antivirus results.
This approach helps identify false positives and negatives, providing a comprehensive analysis solely based on the file content.
Moreover, the LLM model’s code analysis may contain errors and lack accuracy.
Security analysts should illuminate the Code Insight data properly while incorporating contextual data associated with the analyzed file.
Incorporating LLMs into code analysis tools is a significant breakthrough, as this will significantly enhance the platform’s efficiency.
“VirusTotal plans to broaden the scope of its new feature by adding additional file formats to its list of supported files shortly,” Says Virustotal report.
By employing more than 70 antivirus scanners and domain blocklisting services, it inspects doubtful files and URLs for malicious content such as:-
Different AI models can perform this analysis with varying levels of accuracy and scope.
Still, VirusTotal’s Code Insight is most valuable for its ability to scale this analysis via its platform.
The VirusTotal Intelligence service allows the gathering and utilizing results on a large scale, enabling the study of individual code samples and their accumulation.
Therefore, security teams can rapidly and efficiently analyze considerable amounts of code, detecting potential threats and strengthening their security posture.
Building Your Malware Defense Strategy – Download Free E-Book

Read the full article here

