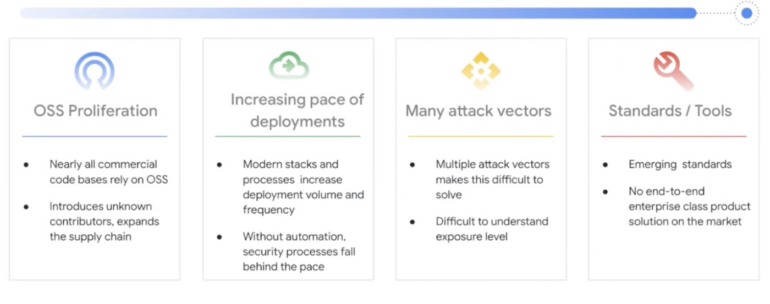
Google Cloud is making it’s Assured Open Source Software (Assured OSS) service available for Java and Python ecosystems without charge in response to the rising dangers associated with dependency on open-source software.
According to a 2023 study by Synopsys, 84% of open-source software codebases featured at least one known vulnerability – a roughly 4% rise from the previous year — and 48% contained a high-risk vulnerability.
By routinely scanning and analyzing some of the most well-known software libraries in the world for vulnerabilities, the Assured Open Source Software (Assured OSS) service aids developers in their defense against supply chain security assaults.
The company partially developed Assured OSS in May 2022 to address the exponential surge in hacks targeted at open-source vendors.
“Software supply chain attacks targeting open source continue to increase. Secure ingest of open source packages is a widespread challenge for organizations and developers wherever they choose to build code,” Andy Chang, group product manager, security and privacy at Google.
“Google is uniquely positioned to help in this area as we are a long time contributor, maintainer, and user of open source software and have developed a robust set of technology, processes, security capabilities and controls.”
Features of Assured OSS
Google’s Assured OSS programme offers the following code packages, according to Google:
- Are regularly scanned, analyzed, and fuzz-tested for vulnerabilities.
- Have corresponding enriched metadata incorporating Container/Artifact Analysis data.
- Are built with Cloud Build, including evidence of verifiable SLSA compliance.
- Are verifiably signed by Google.
- Are distributed from an Artifact Registry secured and protected by Google.
Securing codebases means identifying potential entry points for hackers and testing software for “corner cases,” or flaws in unexpected places, through crash testing.
“Assured OSS provides value to organizations looking for guidance on which packages are trustworthy within the sprawling open source universe,” said Andy Chang.
“But it’s important that they also have the tools in place to keep problematic components from entering their development pipeline, as well as continuously monitor previously trustworthy components for any newly discovered issues.”
Also, the SLSA framework, which stands for “supply chain levels for software artifacts,” adds assurance to the software development lifecycle.
He claimed that by adding new security rules to address the most prevalent vulnerabilities in the current landscape, SLSA formalizes the criteria for software supply chain integrity and assists organizations in taking small steps toward a more secure software supply chain.
Chang added that having richer metadata that includes information from container analysis is essential because “the more you know about the open source software being used, the better choices DevSecOps teams have related to policy enforcement and risk.”
“Because the metadata is signed, customers can have confidence that the details contained in the metadata — including how the package is built, the build steps, which build tools touched the code, and which security scan tools were run on the code — are all as they were when Google created them.”
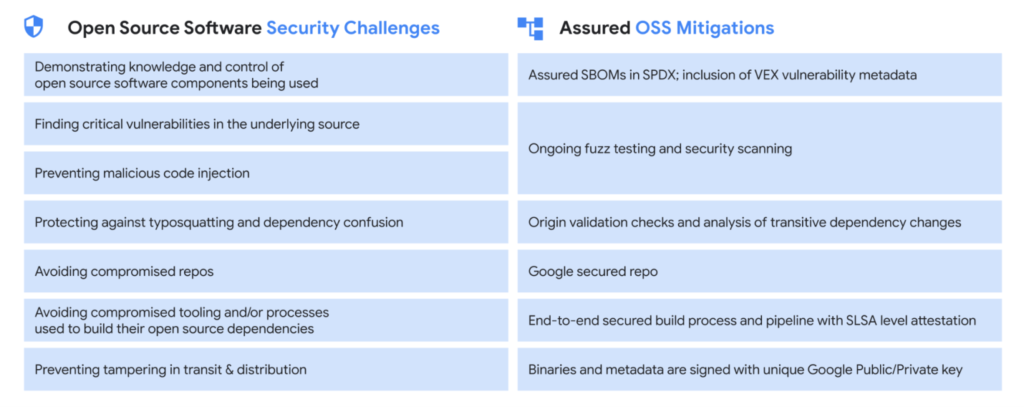
Google claims that the Assured OSS programme will allow organizations to obtain OSS packages from a trusted source and know exactly what the software contains because it includes Google’s software bill of materials or SBOMs.
According to the company, the Assured OSS project comprises 1,000 Java and Python packages and eliminates the need for DevOps teams to set up and manage their own OSS security operations.
Building Your Malware Defense Strategy – Download Free E-Book

Read the full article here