A previously undocumented Android malware campaign has been observed leveraging money-lending apps to blackmail victims into paying up with personal information stolen from their devices.
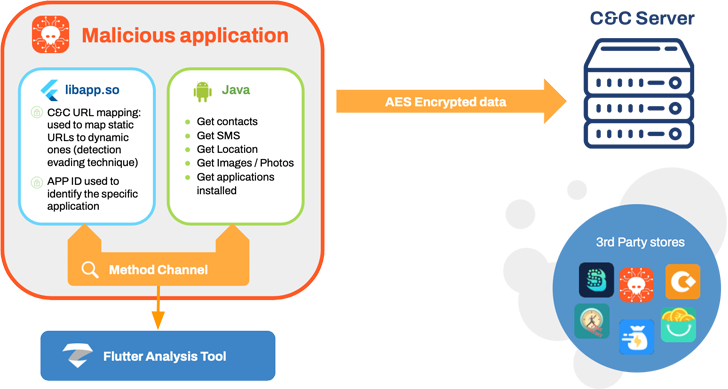
Mobile security company Zimperium dubbed the activity MoneyMonger, pointing out the use of the cross-platform Flutter framework to develop the apps.
MoneyMonger “takes advantage of Flutter’s framework to obfuscate malicious features and complicate the detection of malicious activity by static analysis,” Zimperium researchers Fernando Sanchez, Alex Calleja , Matteo Favaro, and Gianluca Braga said in a report shared with The Hacker news.
“Due to the nature of Flutter, the malicious code and activity now hide behind a framework outside the static analysis capabilities of legacy mobile security products.”
The campaign, believed to be active since May 2022, is part of a broader effort previously disclosed by Indian cybersecurity firm K7 Security Labs.
None of the 33 apps used in the deceptive scheme have been distributed through the Google Play Store. The money lending applications, instead, are available through unofficial app stores or sideloaded to the phones via smishing, compromised websites, rogue ads, or social media campaigns.
Once installed, the malware poses a risk as it’s designed to prompt the users to grant it intrusive permissions under the pretext of guaranteeing a loan, and harvest a wide range of private information.
The collected data – which includes GPS locations, SMSes, contacts, call logs, files, photos, and audio recordings – is then used as a pressure tactic to force victims into paying excessively high-interest rates for the loans, sometimes even in cases after the loan is repaid.
To make matters worse, the threat actors subject the borrowers to harassment by threatening to reveal their information, call people from the contact list, and send abusive messages and morphed photos from the infected devices.
The scale of the campaign is unclear owing to the use of sideloading and third-party app stores, but the rogue apps are estimated to have racked up over 100,000 downloads through the distribution vector.
“The extremely novel MoneyMonger malware campaign highlights a growing trend by malicious actors to use blackmail and threats to scam victims out of money,” Richard Melick, director of mobile threat intelligence at Zimperium, said in a statement.
“Quick loan programs are often full of predatory models, such as high-interest rates and payback schemes, but adding blackmail into the equation increases the level of maliciousness.”
Google, in a comment shared with The Hacker News, reiterated that the identified malicious apps are not downloadable from the Play Store and that Google Play Protect helps notify users about potentially harmful apps.
“Google Play Protect checks Android devices with Google Play Services for potentially harmful apps from other sources,” the company said. “Google Play Protect will warn users that attempt to install or launch apps that have been identified to be malicious.”
The findings come two weeks after Lookout discovered nearly 300 mobile loan applications on Google Play and Apple’s App Store that collectively have more than 15 million downloads and have been found engaging in predatory behavior.
These apps not only exfiltrate extraordinary volumes of user data but also come with hidden fees, high-interest rates, and payment terms that are used to strong-arm victims for payment on fraudulent loans.
“They exploit victims’ desire for quick cash to ensnare borrowers into predatory loan contracts and require them to grant access to sensitive information such as contacts and SMS messages,” Lookout noted late last month.
Developing countries are a prime target for dodgy loan apps, as digital lending has seen explosive growth in markets like India, where people are unwittingly turning to such platforms after being turned away by banks for failing to meet income requirements.
The exploitative nature of the personal loan terms has also led to multiple incidents of suicides in the country, prompting the Indian government to initiate work on an allowlist of legal digital lending apps that are permitted in app stores.
Google, in August, disclosed it had removed more than 2,000 credit disbursement apps from its Play Store in India since the start of the year for violating its terms.
The government has also sought urgent strict action by law enforcement agencies against loan apps, a majority of them Chinese-controlled, that have been found to use harassment, blackmail, and harsh recovery techniques.
Read the full article here