In 2023, the global average cost of a data breach reached $4.45 million. Beyond the immediate financial loss, there are long-term consequences like diminished customer trust, weakened brand value, and derailed business operations.
In a world where the frequency and cost of data breaches are skyrocketing, organizations are coming face-to-face with a harsh reality: traditional cybersecurity measures might not be cutting it anymore.
Against this backdrop, businesses must find ways to strengthen their measures to safeguard precious data and critical assets. At the heart of this shift lies a key strategy: continuous monitoring.
Understanding Continuous Security Monitoring in Cybersecurity
Continuous monitoring is a dynamic approach that encompasses several techniques to fulfil a multi-layered defense strategy. These techniques can include:
Unlike point-in-time assessments, which are analogous to taking a photo of your security posture, continuous monitoring is like a 24/7 live stream. It proactively scouts for vulnerabilities, irregularities, misconfigurations, and potential threats, ensuring swift detection and response.
Continuous Security Monitoring for Web Applications
Protecting business applications should be a central component of any effective cybersecurity strategy. Not only are they a tempting target for cybercriminals, but they are also increasingly difficult to protect. According to a recent report, based on analysis of 3.5 million business assets, the vast majority (74%) of internet-exposed web apps containing personal identifiable information (PII) are vulnerable to a cyberattack.
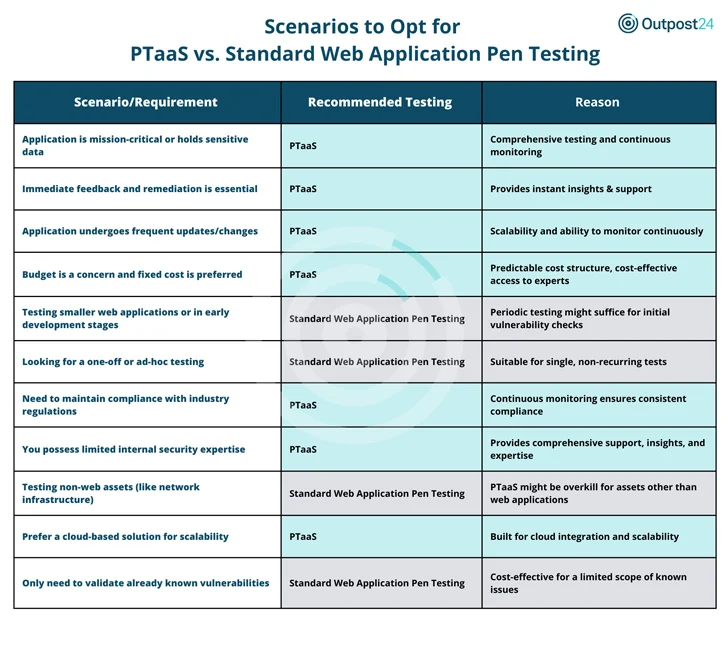
When it comes to protecting their web application, organizations often grapple with a critical choice: a pen testing as a service (PTaaS) solution or the standard (periodic or ad-hoc) pen test. The choice boils down to your organization’s specific needs. Both tools have their merits; it’s about aligning the tool with the task at hand, ensuring you’re always ahead in the cybersecurity game.
The Benefits of PTaaS
- In environments where apps are crucial or handle sensitive data a PTaaS solution and its continuous monitoring is a non-negotiable. It offers ongoing protection against evolving vulnerabilities.
- On the budget front, PTaaS offers a predictable cost model, making it a cost-effective route to high-level security expertise.
- For organizations limited in security manpower, PTaaS fills the gap, providing robust support and direct access to security experts.
The Benefits of the Standard Pen Testing
- For newer or smaller web apps, occasional checks might be enough, which is where the standard pen test steps in.
- Have a one-time need, like a specific security verification? standard pen testing is your best bet. It’s also more suited for tasks centered on non-web assets, like network infrastructure.
- If you’re strictly looking to validate known vulnerabilities, standard pen testing offers a focused, cost-effective solution.
The Broader Landscape of Continuous Monitoring
Outpost24 identifies security gaps across your entire attack surface and helps you prioritize vulnerabilities to optimize your cybersecurity posture and reduce exposure.
- Outscan NX (RBVM): Vulnerability management with real-world threat intelligence to focus remediation and reduce business risk.
- SWAT (PTaaS): Manual testing and automated scanning with access to security experts for your agile development cycles.
- Sweepatic (EASM): Attack surface discovery and monitoring in real-time with actionable insights.
- Threat Compass (Cyber Threat Intelligence): Targeted and actionable intelligence for faster threat detection and incident response.
The digital age demands a rethink of our cybersecurity paradigms. The rising costs and risks associated with data breaches make it clear: continuous security monitoring isn’t just an option, it’s a necessity. With the above solutions, Outpost24 offers a robust toolkit to navigate this new cybersecurity landscape.
Read the full article here

